Last week, we examined the cybersecurity and geopolitical dynamics facing multinationals in the Indo-Pacific, including the use of “gray zone” tactics that threaten private networks and undermine democratic stability.
This week, we provide our assessment of the 2024 election security threat landscape and offer free SentinelOne assistance to state and local governments on the front lines of democracy.
Please subscribe to read future issues — and forward this newsletter to interested colleagues.
Contact us directly with any comments or questions: [email protected]
PinnacleOne ExecBrief | State and Local Election Security Advisory
With less than 50 days until the 2024 Presidential Election, it is crunch time for election officials, state and local security teams, technology providers, federal support agencies, and cybersecurity firms alike. This PinnacleOne Advisory provides our assessment of the 2024 election security threat landscape facing state and local officials across the country and offers free SentinelOne assistance until the election.
As CISA Director Jen Easterly recently affirmed, “election infrastructure has never been more secure, and the election stakeholder community has never been more prepared. However, the threat environment that they’re facing has never been as complex as it is now – whether that’s cyber threats or physical threats.”
Cyber Assistance from SentinelOne
At SentinelOne, we understand the urgency of protecting critical infrastructure during elections. Our world-leading Security AI platform and strategic advisory services are designed to help election officials detect, respond to, and mitigate both known and emerging threats. Our team of experts is ready to assist you in enhancing your security posture, conducting thorough program assessments, and providing real-time threat monitoring to ensure uninterrupted operations during this crucial election period.
For state and local governments seeking additional support, we offer free Managed Services from SentinelOne that seamlessly integrate into your existing environment, including:
- Vigilance MDR for essential 24×7 detection and response coverage for endpoints
- WatchTower Threat Hunting to help you stay ahead of attacks
- Purple AI, the industry’s most advanced AI security analyst
Together, we can strengthen election infrastructure and ensure that voting operations remain secure and resilient in the face of evolving threats. Please visit our website here for more information: https://www.sentinelone.com/lp/securing-governments/.
Threat Landscape | What State and Local Officials are Facing
As CISA has reported, America’s adversaries persist in targeting U.S. elections as part of their efforts to “undermine U.S. global standing, sow discord inside the United States, and influence U.S. voters and decision making.” U.S. elections remain an attractive target for both nation-states and cyber criminals and are exposed to both cybersecurity and physical threats.
Cyber Threats
Given the broad and heterogenous organization of U.S. election systems and processes, it is very difficult for a single cyber attack to cause a systemic effect. Nevertheless, there are a range of highly capable nation-state threat actors, cybercriminal groups, and motivated hacktivist groups with an interest in influencing, disrupting, or undermining U.S. elections.
According to the latest Election Security Update from the Office of the Director of National Intelligence (ODNI), the IC “assesses that a diverse, growing, and more capable group of foreign actors is or will likely try to influence our elections this November.” Specifically:
Russia remains the most significant threat, focusing on promoting divisive narratives and targeting specific voter demographics to influence electoral outcomes and diminish U.S. support for Ukraine. Russia’s “Doppleganger” disinformation campaign, exposed by U.S. indictments, involved creating fake news websites and using AI to generate content posing as U.S. citizens. Two individuals linked to Russian state media were charged, and over 30 domains were seized. SentinelOne has previously published reports on Doppleganger’s activity in German politics.
China is more cautious in its approach, focusing on data collection and public opinion monitoring, without overt plans to influence election results, as it perceives little benefit in doing so due to both U.S. political parties aiming to contain China. Chinese government-affiliated actors have used deepfakes, fake news broadcasts, and altered social media posts to spread disinformation. Their campaigns have focused on controversial U.S. domestic issues such as climate change, immigration, and the U.S. government’s response to disasters like the Maui wildfires. These influence efforts aim to exploit political divisions, particularly in battleground states, and gather intelligence on American voters. In the U.K., Chinese hackers were behind a significant cyberattack on the Electoral Commission, gaining access to the personal information of millions of British voters.
Iran seeks to exploit U.S. societal tensions and undermine confidence in democratic institutions, including leveraging issues such as the Israel-Gaza conflict. Iranian cyber actors have adopted Russian tactics, conducting cyber espionage and influence campaigns to undermine U.S. election integrity. In August, federal agencies exposed an Iranian operation targeting Donald Trump’s 2024 campaign, involving the theft of internal documents. Iran also attempted but failed to hack Joe Biden’s campaign. Despite exposure, Iran is expected to continue its efforts using spear-phishing and social media tactics.
The ODNI also flagged the increasing role of AI in influence operations, citing examples from foreign elections where AI-generated synthetic content (e.g., videos, audio) has been used to spread disinformation and manipulate public opinion, such as in Taiwan and India.
Cyber Threat Mitigations
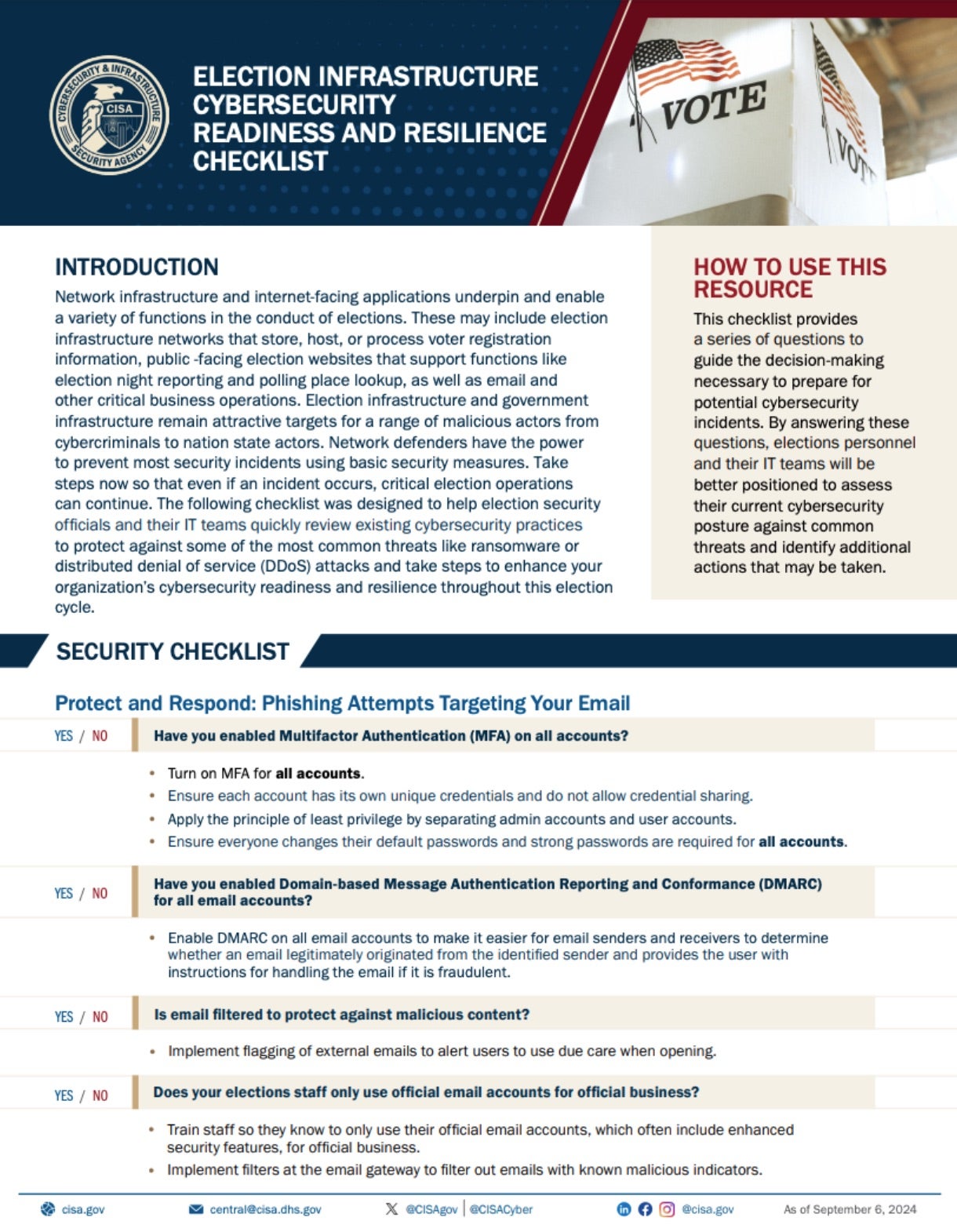
Just as for physical threats, CISA’s Election Infrastructure Cybersecurity Readiness and Resilience Checklist provides a thorough guide for election officials to safeguard election infrastructure from common cybersecurity threats like phishing, ransomware, and DDoS attacks. This checklist helps assess the current cybersecurity posture and outlines proactive measures to enhance resilience.
Threat Actor Tactics
Foreign malign influence operations represent a significant threat to the integrity of democratic processes, particularly in the U.S. elections. These operations are orchestrated by foreign governments, including the China, the Russian Federation, and the Islamic Republic of Iran, which exploit sociopolitical divisions to undermine confidence in democratic institutions and sway public opinion.
According to the ODNI, these adversaries use a wide range of tactics, from disinformation campaigns to cyber-enabled operations, increasingly leveraging new technologies such as artificial intelligence to amplify their efforts. Threat actor tactics include:
- Disguising Proxy Media – Foreign actors create fake news outlets that blend real and fake content to appear credible, aiming to manipulate public opinion (e.g., Russian-linked sites posing as U.S. local news).
- Voice Cloning – Using AI to fabricate recordings of public figures, misleading audiences (e.g., fake voice recordings of Slovak politicians before elections).
- Cyber-Enabled Operations – Hacking organizations to steal and leak sensitive information as part of influence campaigns (e.g., Russian actors leaking U.S.-UK trade documents before the 2019 British elections).
- Manufacturing False Evidence – Spreading fake reports or documents to incite alarm (e.g., pro-China actors distributing fabricated Taiwanese government documents during Taiwan’s elections).
- Paid Influence – Foreign actors secretly pay influencers or media firms to spread their narratives (e.g., China using media firms to promote content downplaying human rights abuses in Xinjiang).
- Leveraging Social Media – Using platforms with weak content moderation to spread divisive narratives (e.g., Russian actors utilizing Telegram to promote pro-Russian content and amplify political divisions).
Recommendations
As the 2024 U.S. Election approaches, safeguarding the integrity of election infrastructure is a critical priority for election officials, state and local security teams, technology providers, and federal agencies, as well as cybersecurity firms like SentinelOne. With a heightened threat landscape — spanning both physical and cyber risks — timely action is essential to:
- Strengthen Cybersecurity Defenses – Implement robust email filtering, phishing detection, and MFA for all official accounts. Utilize CISA’s Election Infrastructure Cybersecurity Readiness and Resilience Checklist to defend against ransomware and DDoS attacks. Train all election staff to recognize and respond to potential cyber threats, such as phishing or disinformation campaigns.
- Engage Federal and Local Resources – Collaborate with CISA, the FBI, and state agencies to leverage tools like cyber hygiene scanning, vulnerability assessments, and threat monitoring. A coordinated effort is key to identifying and mitigating potential risks before they impact election operations.
- Enhance Physical Security Measures – Utilize CISA’s Physical Security Checklist to reinforce polling locations, voting equipment storage facilities, and transportation networks. Prepare emergency response plans and train election workers to handle physical threats, including potential violence or sabotage attempts.
- Test and Update Incident Response Plans – Regularly test contingency plans, focusing on ransomware and DDoS attack responses. Ensure election systems can operate through disruptions by using offline backups, provisional ballots, and alternative communication channels.
If you are a state and local government official in need of extra assistance, please reach out: https://www.sentinelone.com/lp/securing-governments/


