LABScon24 Replay | Kryptina RaaS: From Unsellable Cast-off to Enterprise Ransomware
Jim Walter reveals how a recent leak provided insight into how Kryptina RaaS has been adapted for use in enterprise attacks.
Read More
Jim Walter reveals how a recent leak provided insight into how Kryptina RaaS has been adapted for use in enterprise attacks.

Kim Zetter interviews David Weston on topics such as the fallout from the CrowdStrike outage, Windows Recall and improving Microsoft security.

Kristin Del Rosso & Madeleine Devost explore the growing trend of foreign ownership of farmland and its implications for national security.

Chinese foreign direct investment should trigger American national security concerns, but much of it doesn’t. Elly Rostoum reveals why.

Martin Wendiggensen reveals how disinformation shaped Taiwan’s election, and how AI-powered research uncovered hidden influences on voter behavior.

Max Smeets explores how ransomware groups leverage public reporting and why we must disrupt the trust dynamic between threat actors and victims.

Kymberlee Price reveals the technical chaos facing SMBs as they struggle with solutions aimed at bigger fish in the face of expanding crimeware.

Binarly’s Alex Matrosov and Fabio Pagani present PKfail, a firmware supply-chain security issue affecting major device vendors and hundreds of device models.
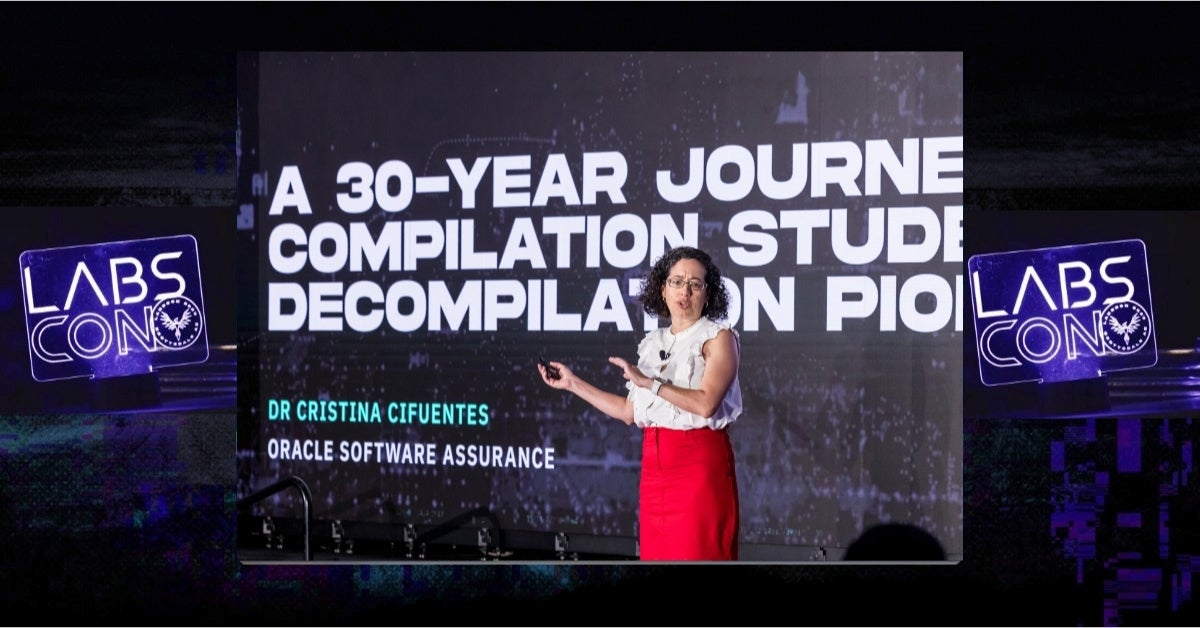
Dr. Cristina Cifuentes, known as the Mother of Decompilation, reflects on three decades of innovation in reverse engineering in her LABScon 2024 keynote.

Zuzana Hromcová explores how Iran-aligned APT OilRig targets healthcare and local governments with a stream of updated and newly developed tools.