
LABScon24 Replay | The Real AI Race: Disinformation in the Taiwanese Election
Martin Wendiggensen reveals how disinformation shaped Taiwan’s election, and how AI-powered research uncovered hidden influences on voter behavior.
Read More

Martin Wendiggensen reveals how disinformation shaped Taiwan’s election, and how AI-powered research uncovered hidden influences on voter behavior.

Max Smeets explores how ransomware groups leverage public reporting and why we must disrupt the trust dynamic between threat actors and victims.

Kymberlee Price reveals the technical chaos facing SMBs as they struggle with solutions aimed at bigger fish in the face of expanding crimeware.

Binarly’s Alex Matrosov and Fabio Pagani present PKfail, a firmware supply-chain security issue affecting major device vendors and hundreds of device models.
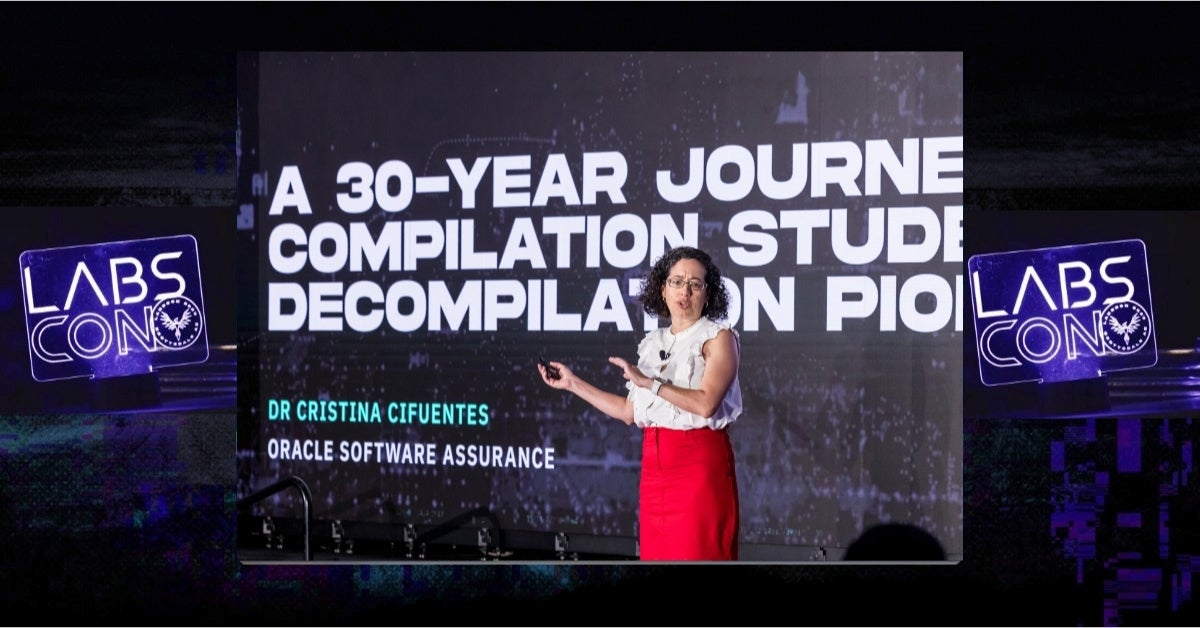
Dr. Cristina Cifuentes, known as the Mother of Decompilation, reflects on three decades of innovation in reverse engineering in her LABScon 2024 keynote.

Zuzana Hromcová explores how Iran-aligned APT OilRig targets healthcare and local governments with a stream of updated and newly developed tools.
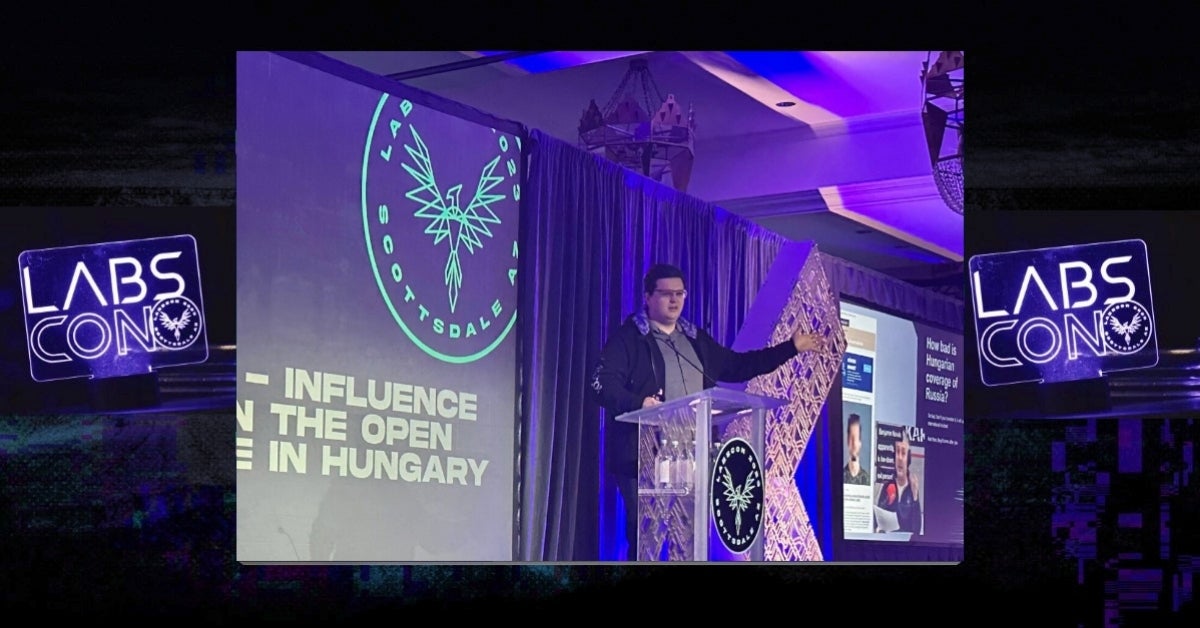
As electorates across the US and Europe go to the polls in 2024, this must-see talk on large-scale state influence operations could hardly be more timely or relevant.

Greg Lesnewich takes us on a tour of North Korean APTs targeting macOS and explores techniques for tracking an increasingly active threat cluster.
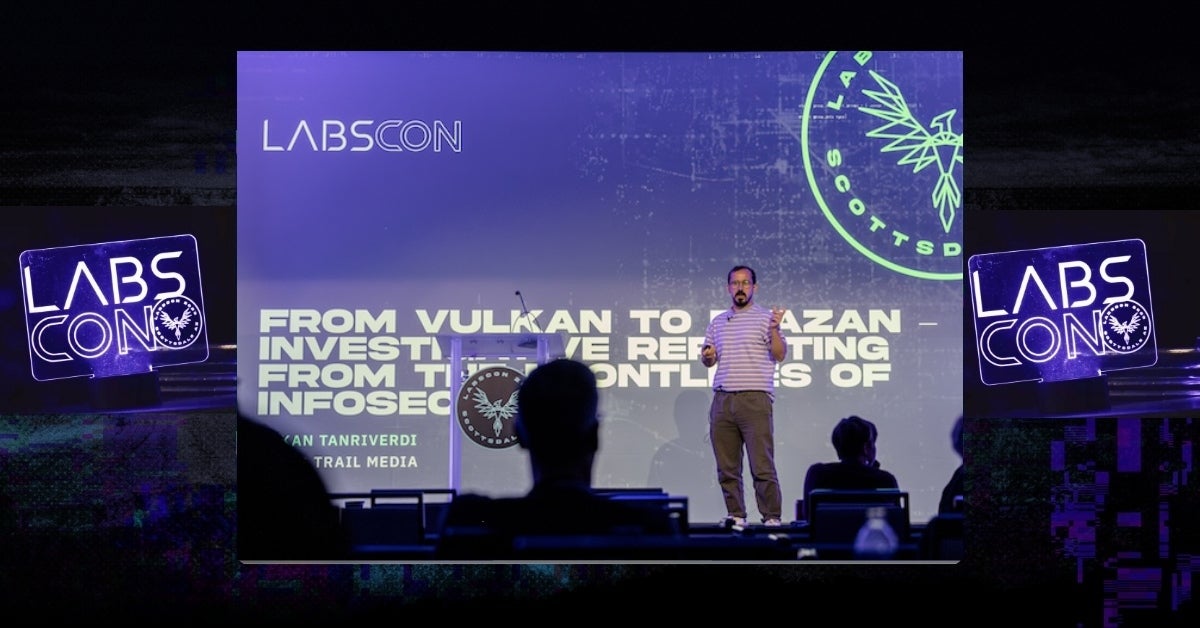
Covering investigations into Turla, Magna Bear and REvil, this talks offers a fascinating insight into how researchers unmask threat actor identities.

Take a unique look inside Iran's drone and missile program as Adam Rawnsley charts the rise of Mado, a key IRGC drone company.