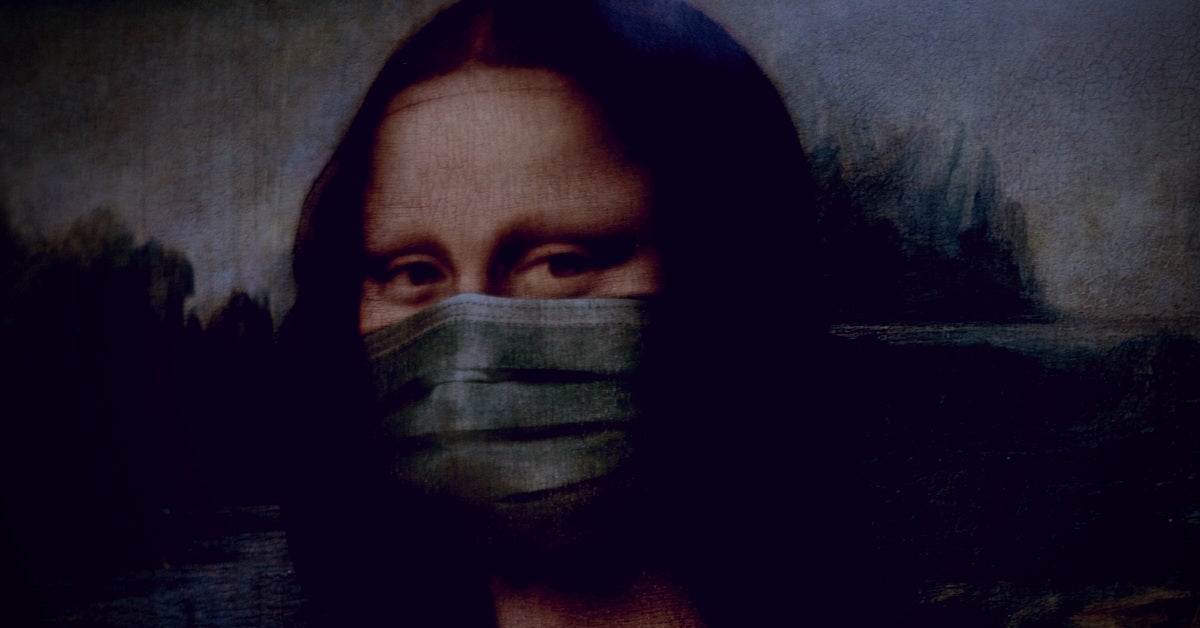
Threat Intel | Cyber Attacks Leveraging the COVID-19/CoronaVirus Pandemic
At Sentinel Labs, we have been closely tracking adversarial behavior as it pertains to COVID-19/Coronavirus. To date, we have observed a significant number of malware campaigns, spam campaigns, and outright…
Read More