
Censorship as a Service | Leak Reveals Public-Private Collaboration to Monitor Chinese Cyberspace
Data leak reveals how a top tier cybersecurity vendor helps the PRC enforce content monitoring and manipulation of public opinion in China.
Read More

Data leak reveals how a top tier cybersecurity vendor helps the PRC enforce content monitoring and manipulation of public opinion in China.

SentinelLABS has observed an active phishing campaign targeting high-profile X accounts to hijack and exploit them for fraudulent activity.

Chinese foreign direct investment should trigger American national security concerns, but much of it doesn’t. Elly Rostoum reveals why.

Martin Wendiggensen reveals how disinformation shaped Taiwan’s election, and how AI-powered research uncovered hidden influences on voter behavior.

Max Smeets explores how ransomware groups leverage public reporting and why we must disrupt the trust dynamic between threat actors and victims.

Kymberlee Price reveals the technical chaos facing SMBs as they struggle with solutions aimed at bigger fish in the face of expanding crimeware.

Threat actors abused Visual Studio Code and Microsoft Azure infrastructure to target large business-to-business IT service providers in Southern Europe.

Binarly’s Alex Matrosov and Fabio Pagani present PKfail, a firmware supply-chain security issue affecting major device vendors and hundreds of device models.
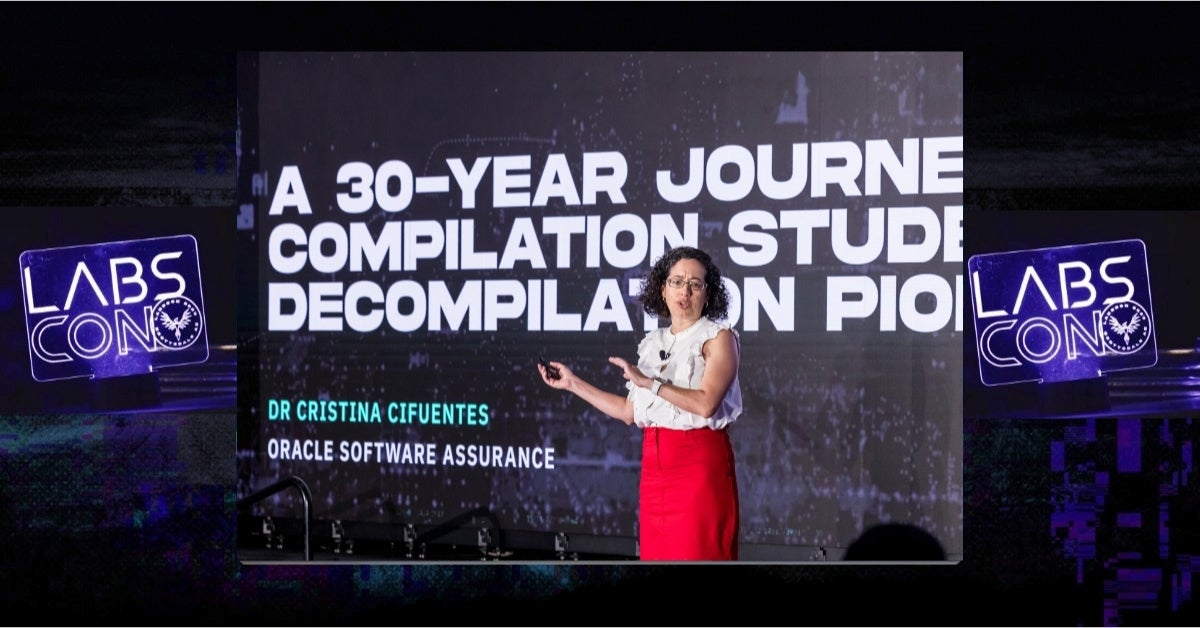
Dr. Cristina Cifuentes, known as the Mother of Decompilation, reflects on three decades of innovation in reverse engineering in her LABScon 2024 keynote.

A loose collective of mostly low-skilled actors, CyberVolk absorbs and adapts a wide array of destructive malware for use against political targets.