The Good
The Biden administration signed a new executive order this week; the latest in an effort to prohibit U.S. government agencies from buying and using commercial spyware operationally. Targeting spyware’s increasing threat to national security and its implication in human rights abuse, the President called for an international coalition focused on combating spyware as a whole.

Governments across the globe have been known to collect troves of sensitive data for law enforcement and intelligence purposes. As use of spyware grew to meet these needs, the tools have inevitably been made available to opposing entities who have used them to meet their goals of abuse and oppression.
Spyware has long been marked as a high-level issue. The order emphasized that commercial spyware poses counterintelligence and security risks to the U.S. government if used by foreign governments or persons to gain access to U.S. computers and its data without authorization. Further, spyware is often used to collect information on political figures, dissents, activists, academics, journalists, or members of marginalized communities for the purpose of intimidation.
While President Biden’s executive order does allow some exceptional use cases, it represents a clear step towards the clamp down on using commercial spyware for non-testing purposes. The impact of modern-day technology on government systems and human rights continues to grow and it is likely that more issues will arise from these intersections and highlight the continued need to regulate, oversee, and audit new advancements in technology.
The Bad
A new comprehensive toolset is being sold to threat actors through private Telegram channels, SentinelLabs researchers reported this week. Dubbed ‘AlienFox’, this toolset enables actors to perform scans for misconfigured servers and extract API keys and secrets from AWS, Google, and Microsoft.
Analyzing three versions of AlienFox, researchers noted that the malware is being used to enumerate misconfigured hosts through security scanning services such as LeakIX and SecurityTrails. The AlienFox operators search for vulnerable services that are associated with widely-used frameworks such as Laravel, Drupal, Joomla, Magento, Opencart, Prestashop, and WordPress. Finally, the operators leverage various scripts provided in the toolset to harvest credentials and sensitive data from configuration files that are exposed on compromised servers of cloud-based email platforms.
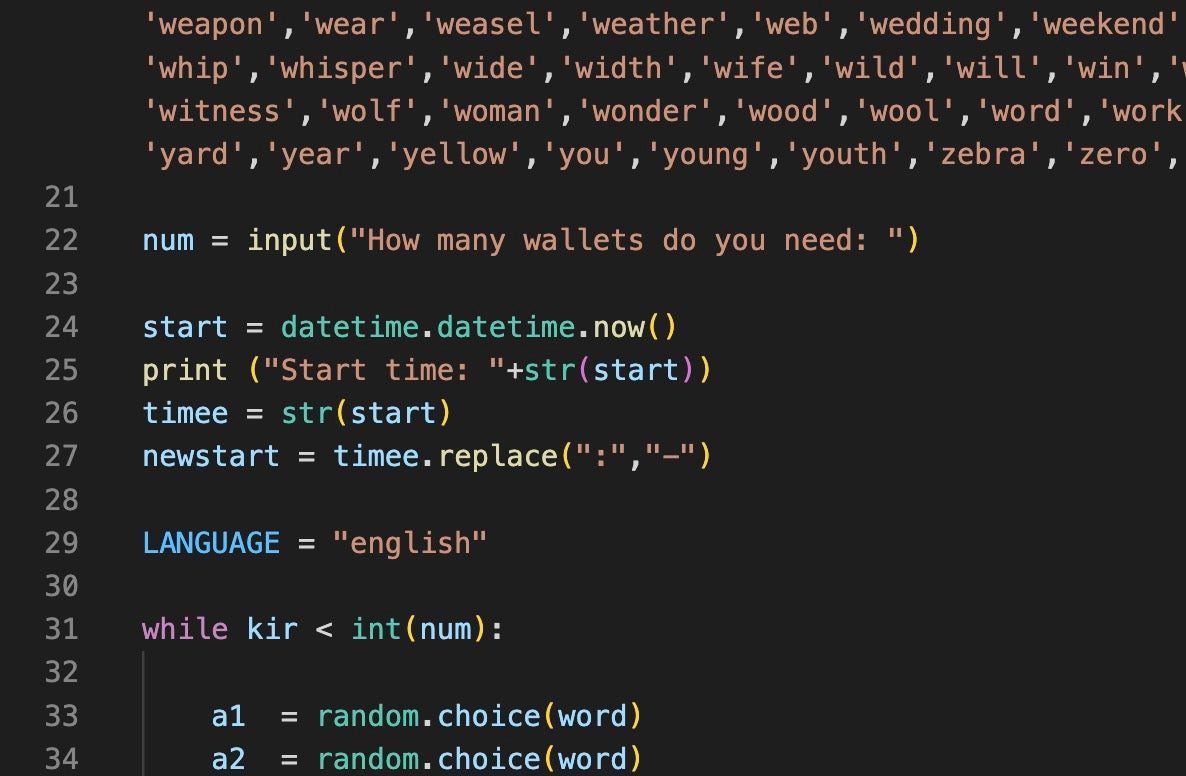
Currently, the most recent version of the toolset has been able to establish persistence on a compromised Amazon Web Services (AWS) account, escalate privileges, and automate a spam campaign. This version also has added an account-checking capability along with an automated cryptocurrency wallet seed cracker for Ethereum and Bitcoin.
The cyber defense community continues to see a rise in attacks on cloud services, particularly for the purpose of expanding subsequent threat campaigns. This is reflected in AlienFox’s highly modular nature, which is observed to be accommodating new features and improvements to attract new buyers and secure renewals from existing ones. Organizations can defend themselves from AlienFox tools by establishing strict configuration management and least privilege practices. Leveraging a Cloud Workload Protection Platform (CWPP) on virtual machines and containers is also key in detecting suspicious activity with the OS before full compromise can occur.
The Ugly
An ongoing cyberattack has occupied the emergency response of international VoIP software developer, 3CX, for the past week as threat actors leverage a trojanized version of their 3CX DesktopApp. The full impact of the continuing attack is unknown so far, though 3CX’s suite of products service over 12 million users in 190 countries with big names like the UK’s National Health Service, Ikea, and American Express as part of their clientele.
A report published by SentinelLabs researchers explains that use of the trojanized 3CX DesktopApp is just the first stage in the multi-stage supply chain attack currently tracked under the campaign name, SmoothOperator.
Infection begins with an MSI installer being downloaded from the official 3CX website or a user pushes an update to an already-installed desktop application. Following initial infection, the actors behind SmoothOperator take advantage of a DLL side-loading technique designed to pull icon file (ICO) payloads appended with Base64 data from GitHub. The malware uses these Base64 strings to download the final payload which then steals credentials and sensitive data housed in popular browsers.
3CX has since released a security alert announcing the imminent release of a new build. In the meantime, the company advises its users to uninstall the desktop app or switch over to the PWA agent in the meantime. In a blog post by 3CX posted the same day, the company divulged that the issue was seemingly associated with one of the bundled libraries compiled into the Electron Windows App via GIT.
The SmoothOperator supply chain campaign is a developing story and more details may come to light in coming days. SentinelOne customers are protected against SmoothOperator with no additional action required.



