GAZPROM Ransomware: In-Depth Analysis, Detection, and Mitigation
What Is GAZPROM Ransomware?
GAZPROM Ransomware emerged in March 2023 with payloads based on re-used code from Conti ransomware. GAZPROM has also been referred to as “Gazprom Locker” and “Gazprom Reborn” in the context of their more recent campaigns. Given the name of the ransomware and some of its associated messaging, we assess there to be a geopolitical slant or motivation behind this threat actor and/or campaign.

What Does GAZPROM Ransomware Target?
GAZPROM ransomware operators do not discriminate when it comes to victimology outside of targeting enterprise and SMB environments. As of this writing, financial institutions have been targeted as have entities in the manufacturing and technology industries.
How Does GAZPROM Ransomware Work?
Initial access in GAZPROM campaigns is achieved via exploitation of publicly-facing and vulnerable applications and devices. Once established, the threat actors combine remote access tools (e.g., Anydesk) with frameworks like Cobalt Strike to further the attack into the target environment.
Analyzed GAZPROM payloads attempt to evade analysis via SLEEP statements. Payloads will attempt to delay execution via this method for up to 300000 milliseconds (5 minutes).
GAZPROM ransomware payloads attempt to identify all locally available drive letters for encryption. This includes those available over SMB via NetShareEnum. GAZPROM Ransomware will attempt to remove Volume Shadow Copies (VSS) via WMIC.EXE. Multiple commands are then used to remove identified VSS in sequence as opposed to using all-encompassing commands in VSSADMIN. When the ransomware is removing these shadow copies, commands similar to the following will be observed:
C:\Windows\System32\wbem\WMIC.exe shadowcopy where "ID='{88888888-8888-8888-8888-888888888888}'" delete
C:\Windows\System32\wbem\WMIC.exe shadowcopy where "ID='{88888889-8888-8888-8888-888888888888}'" delete
C:\Windows\System32\wbem\WMIC.exe shadowcopy where "ID='{88888810-8888-8888-8888-888888888888}'" delete
C:\Windows\System32\wbem\WMIC.exe shadowcopy where "ID='{88855444-9999-8888-8888-888888888888}'" delete
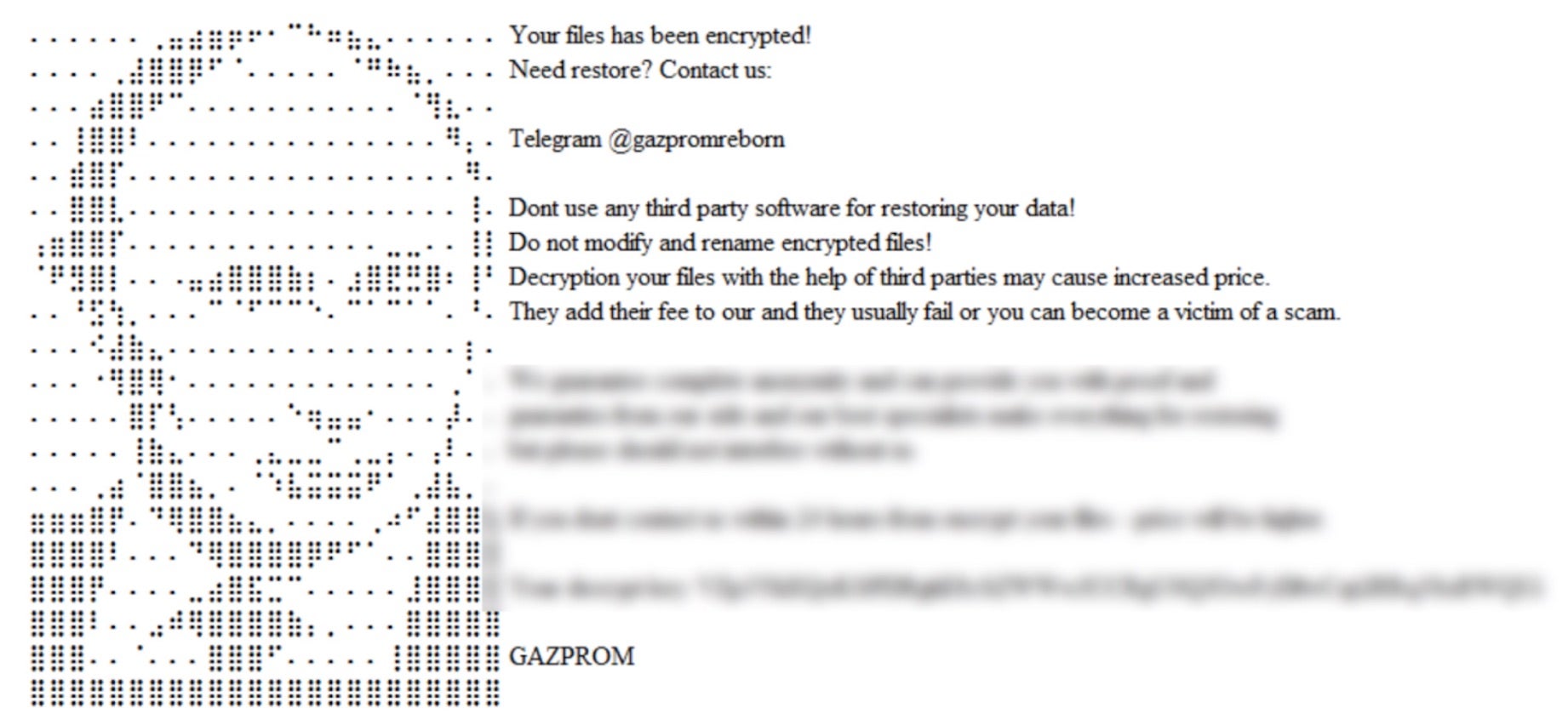
Once encrypted, affected files are modified with a .GAZPROM extension. Ransom notes are dropped in all directories containing encrypted files. These notes are written in .HTA and .HTML format as “GAZPROM_DECRYPT.hta” and “GAZPROM_DECRYPT.html” respectively.
Upon infection, victims are required to contact the attacker via a channel supplied in the ransom note to receive further information. The threat actor has operated multiple support channels throughout the existence of the ransomware. GAZPROM ransom notes indicate that if the victims fail to initiate communication with the attacker within 24 hours, the ransom will be increased.
How to Detect GAZPROM Ransomware
The SentinelOne Singularity XDR Platform can identify and stop any malicious activities and items related to GAZPROM ransomware.
In case you do not have SentinelOne deployed, detecting GAZPROM ransomware requires a combination of technical and operational measures designed to identify and flag suspicious activity on the network. This allows the organization to take appropriate action, and to prevent or mitigate the impact of the ransomware attack.
To detect GAZPROM ransomware without SentinelOne deployed, it is important to take a multi-layered approach, which includes the following steps:
- Use anti-malware software or other security tools capable of detecting and blocking known ransomware variants. These tools may use signatures, heuristics, or machine learning algorithms, to identify and block suspicious files or activities.
- Monitor network traffic and look for indicators of compromise, such as unusual network traffic patterns or communication with known command-and-control servers.
- Conduct regular security audits and assessments to identify network and system vulnerabilities and ensure that all security controls are in place and functioning properly.
- Educate and train employees on cybersecurity best practices, including identifying and reporting suspicious emails or other threats.
- Implement a robust backup and recovery plan to ensure that the organization has a copy of its data and can restore it in case of an attack.
How to Mitigate GAZPROM Ransomware
The SentinelOne Singularity XDR Platform can return systems to their original state using either the Quarantine or Repair.
In case you do not have SentinelOne deployed, there are several steps that organizations can take to mitigate the risk of GAZPROM ransomware attacks:
Educate employees: Employees should be educated on the risks of ransomware, and on how to identify and avoid phishing emails, malicious attachments, and other threats. They should be encouraged to report suspicious emails or attachments, and to avoid opening them, or clicking on links or buttons in them.
Implement strong passwords: Organizations should implement strong, unique passwords for all user accounts, and should regularly update and rotate these passwords. Passwords should be at least 8 characters long, and should include a combination of uppercase and lowercase letters, numbers, and special characters.
Enable multi-factor authentication: Organizations should enable multi-factor authentication (MFA) for all user accounts, to provide an additional layer of security. This can be done through the use of mobile apps, such as Google Authenticator or Microsoft Authenticator, or through the use of physical tokens or smart cards.
Update and patch systems: Organizations should regularly update and patch their systems, to fix any known vulnerabilities, and to prevent attackers from exploiting them. This includes updating the operating system, applications, and firmware on all devices, as well as disabling any unnecessary or unused services or protocols.
Implement backup and disaster recovery: Organizations should implement regular backup and disaster recovery (BDR) processes, to ensure that they can recover from ransomware attacks, or other disasters. This includes creating regular backups of all data and systems, and storing these backups in a secure, offsite location. The backups should be tested regularly, to ensure that they are working, and that they can be restored quickly and easily.