BianLian Ransomware: In-Depth Analysis, Detection, and Mitigation
What Is BianLian Ransomware?
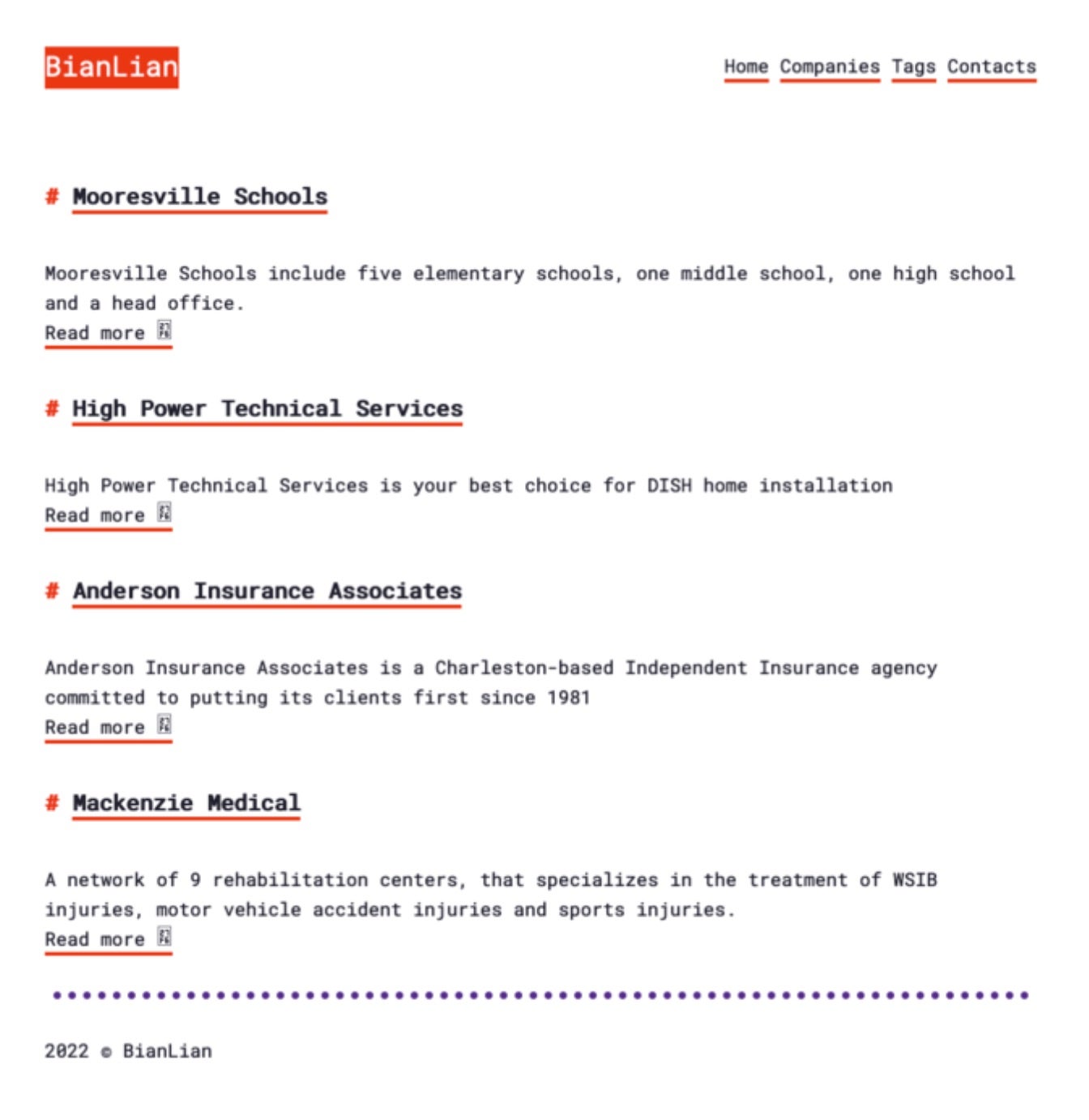
BianLian ransomware operations began in late 2021. Attacks and techniques continue to evolve into 2023. The group practices multi-pronged extortion, demanding payment for a decryptor, as well as the non-release of stolen data. The ransomware group hosts a public, TOR-based, blog to post victim identities and stolen data. Somewhat unique to BianLian at the time of their launch was their inclusion of an I2P mirror for their blog.
What Does BianLian Ransomware Target?
The BianLian group targets multiple industries with little to no discrimination. This includes attacks on healthcare, education, and government entities.
How Does BianLian Ransomware Work?
The group is quick to adopt new tactics and pivot to new lures to ensure successful distribution of their malware. Current BianLian ransomware payloads are written in Go.
Initial access is achieved through exploitation of vulnerabilities on exposed systems and services. These include exploits against RDP, SonicWall VPN devices as well as the ProxyShell vulnerabilities.
BianLian-associated actors make extensive use of LOLBins and COTS (commercial off-the-shelf) tools to evade detection and stealthiness where possible. This includes extensive use of PowerShell, WMIC, WinRM, TightVNC and Non-Sucking Service Manager (NSSM) for their traversal and persistence needs.
The group is also adept at targeting and disabling security tools via their own specific uninstallation and decommission commands. Specific, tailored commands have been observed targeting Windows Defender and Sophos endpoint products for evasion. Encryption is handled within standard Go libraries and all known versions of BianLian contain hard coded lists of extensions or paths to exclude from or include in the encryption process.
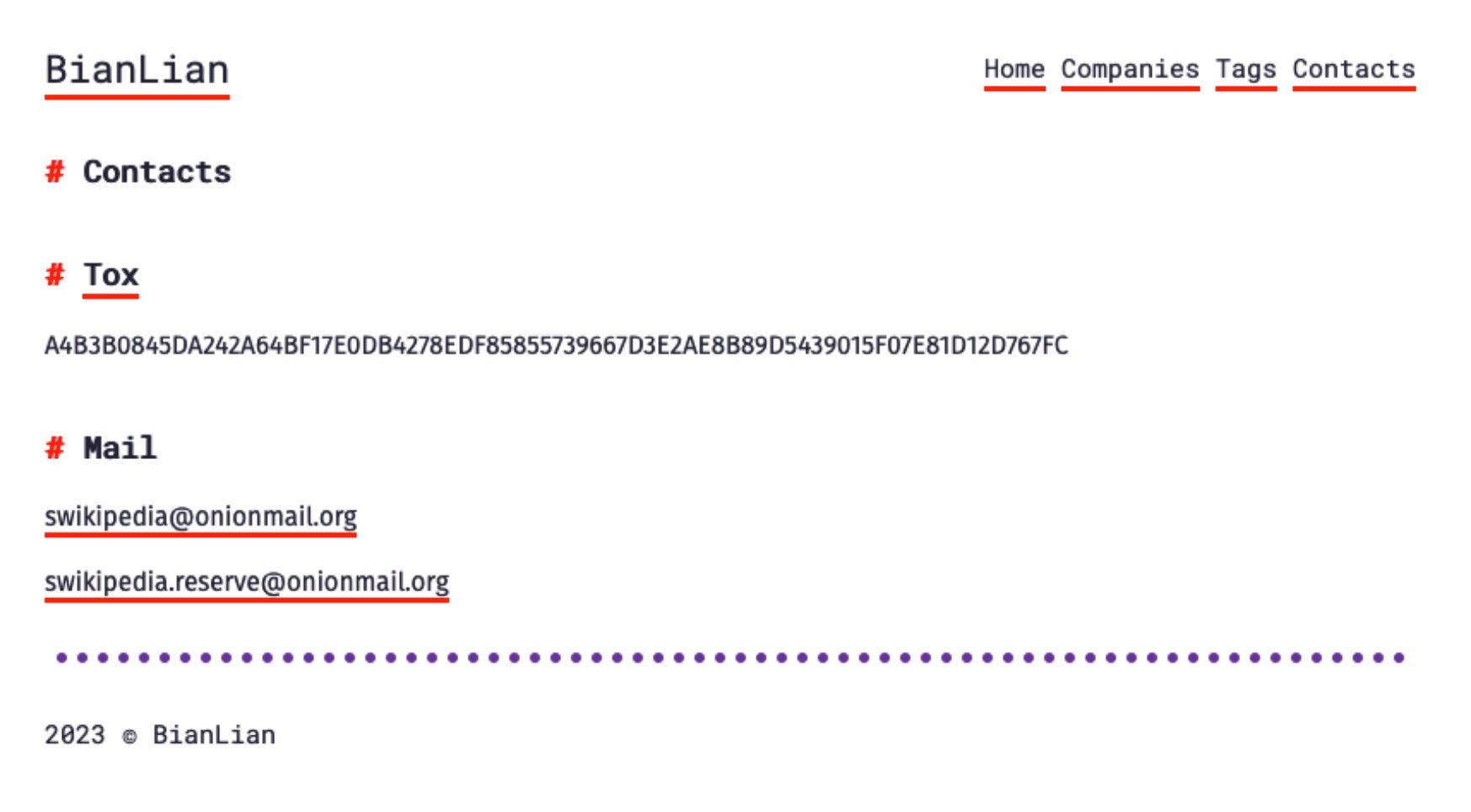
BianLian is extremely rapid. Full disk encryption can take mere minutes if not seconds. Victims are fully encrypted before they notice that something untoward is occuring. BianLian victims are instructed to engage the attackers via their qTOX messenger or secure onionmail addresses.
How to Detect BianLian Ransomware
The SentinelOne Singularity XDR Platform can identify and stop any malicious activities and items related to BianLian Ransomware.
In case you do not have SentinelOne deployed, detecting BianLian ransomware requires a combination of technical and operational measures designed to identify and flag suspicious activity on the network. This allows the organization to take appropriate action, and to prevent or mitigate the impact of the ransomware attack.
To detect BianLian ransomware without SentinelOne deployed, it is important to take a multi-layered approach, which includes the following steps:
- Use anti-malware software or other security tools capable of detecting and blocking known ransomware variants. These tools may use signatures, heuristics, or machine learning algorithms, to identify and block suspicious files or activities.
- Monitor network traffic and look for indicators of compromise, such as unusual network traffic patterns or communication with known command-and-control servers.
- Conduct regular security audits and assessments to identify network and system vulnerabilities and ensure that all security controls are in place and functioning properly.
- Educate and train employees on cybersecurity best practices, including identifying and reporting suspicious emails or other threats.
- Implement a robust backup and recovery plan to ensure that the organization has a copy of its data and can restore it in case of an attack.
How to Mitigate BianLian Ransomware
The SentinelOne Singularity XDR Platform can return systems to their original state using either the Repair or Rollback feature.
In case you do not have SentinelOne deployed, there are several steps that organizations can take to mitigate the risk of BianLian ransomware attacks:
Educate employees: Employees should be educated on the risks of ransomware, and on how to identify and avoid phishing emails, malicious attachments, and other threats. They should be encouraged to report suspicious emails or attachments, and to avoid opening them, or clicking on links or buttons in them.
Implement strong passwords: Organizations should implement strong, unique passwords for all user accounts, and should regularly update and rotate these passwords. Passwords should be at least 8 characters long, and should include a combination of uppercase and lowercase letters, numbers, and special characters.
Enable multi-factor authentication: Organizations should enable multi-factor authentication (MFA) for all user accounts, to provide an additional layer of security. This can be done through the use of mobile apps, such as Google Authenticator or Microsoft Authenticator, or through the use of physical tokens or smart cards.
Update and patch systems: Organizations should regularly update and patch their systems, to fix any known vulnerabilities, and to prevent attackers from exploiting them. This includes updating the operating system, applications, and firmware on all devices, as well as disabling any unnecessary or unused services or protocols.
Implement backup and disaster recovery: Organizations should implement regular backup and disaster recovery (BDR) processes, to ensure that they can recover from ransomware attacks, or other disasters. This includes creating regular backups of all data and systems, and storing these backups in a secure, offsite location. The backups should be tested regularly, to ensure that they are working, and that they can be restored quickly and easily.
BianLian Ransomware FAQs
What is BianLian ransomware?
BianLian is a double extortion ransomware attack. It encrypts files and threatens to leak stolen information. The ransomware appends the .bianlian extension and targets VMware ESXi servers. Victims are redirected to a Tor negotiation page.
Which sectors and regions have been targeted by BianLian ransomware?
BianLian attacks healthcare, manufacturing, and technology firms in the U.S., U.K., and Germany. It recently attacked mid-sized organisations with hybrid cloud infrastructure. The group does not hit targets in Russia and its allies.
How does BianLian ransomware encrypt files, and what file extension does it append?
BianLian uses ChaCha20 encryption for speed and stealth. It appends the .bianliann extension and first encrypts virtual machine files. Ransomware leaves README_FOR_DECRYPT.txt notes in every directory.
What methods does BianLian ransomware use to propagate within networks?
BianLian uses Fortinet and Citrix unpatchед vulnerabilities for initial access. Living-off-the-Land binaries like WMI are used for lateral movement. The ransomware obtains privilege elevation through Windows LSASS exploits.
How can organisations detect an ongoing BianLian ransomware attack?
Look for unusual WMI or PowerShell activity. Look for an unusually high number of files with bianlian appended. Security tools may flag attempts to dump LSASS memory. Look for unauthorised cloud storage bucket access.
What steps should be taken immediately after a BianLian ransomware infection?
Shut down infected virtual machines to limit encryption. Disable internet access to avoid data exfiltration. Take logs for threat hunting. If sensitive data is leaked, use the services of a ransomware negotiation specialist. Reinstall compromised systems from scratch.
How can organisations restore data encrypted by BianLian ransomware?
Use permanent cloud backups saved in isolated accounts. Certain decryption software programs function on older BianLian versions. In negotiations, employ intermediaries for cost-effectiveness. Carefully test restored documents before resuming use.