CrossLock Ransomware: In-Depth Analysis, Detection, and Mitigation
What Is CrossLock Ransomware?
CrossLock ransomware emerged in early 2023 as a multi-extortion group with a TOR-based blog site hosting victim names and data. CrossLock ransomware payloads are written in Go. The payloads contain some more advanced features including an expanded command-line syntax, as well as event tracing bypasses (ETW bypasses).

What Does CrossLock Ransomware Target?
To date, CrossLock ransomware attacks have been focused on targets in South America. The group is known to target entities within the manufacturing and agriculture/farming industries.
How Does CrossLock Ransomware Work?
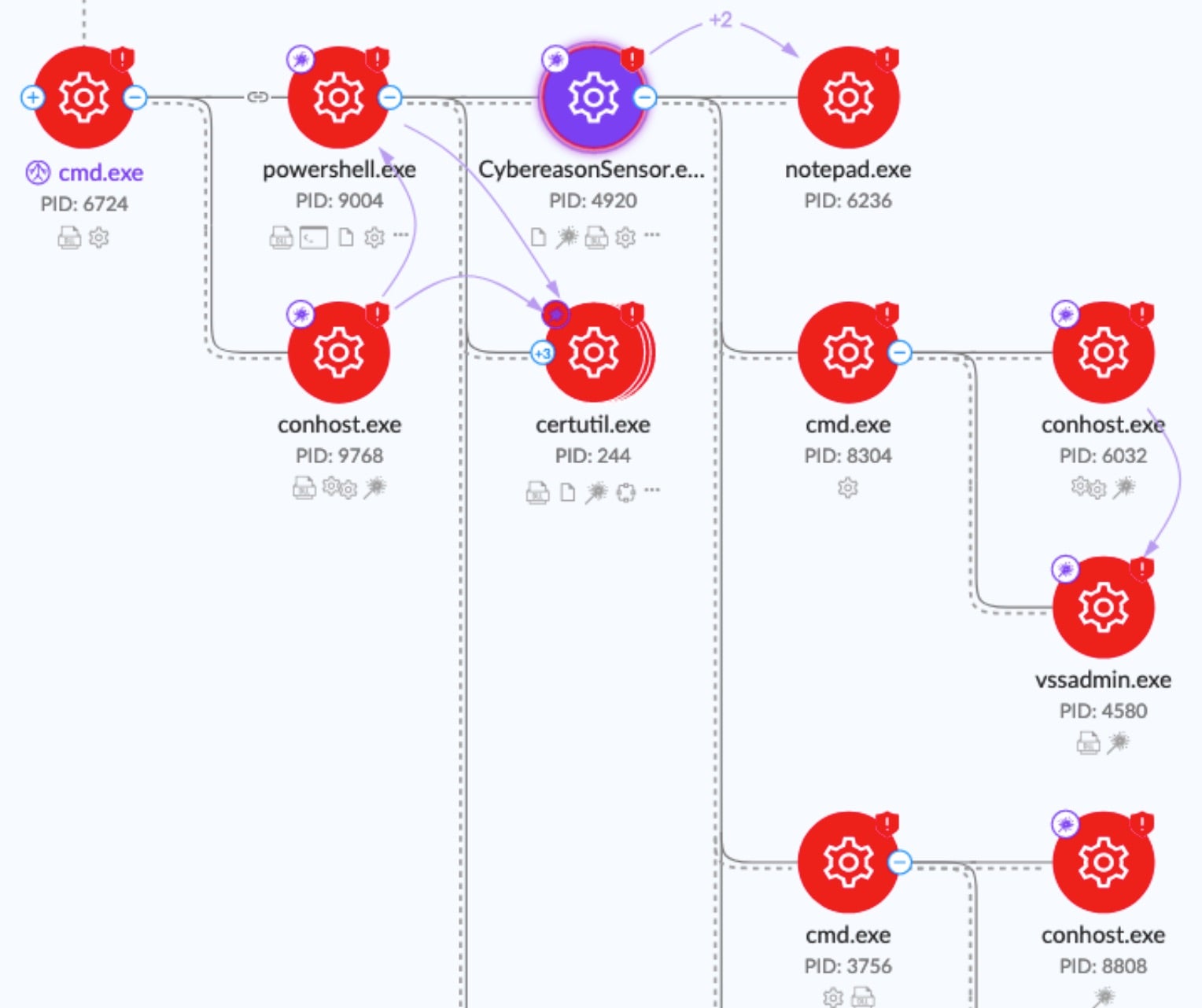
Recent CrossLock ransomware payloads mimic processes from Cybereason, an endpoint security company.
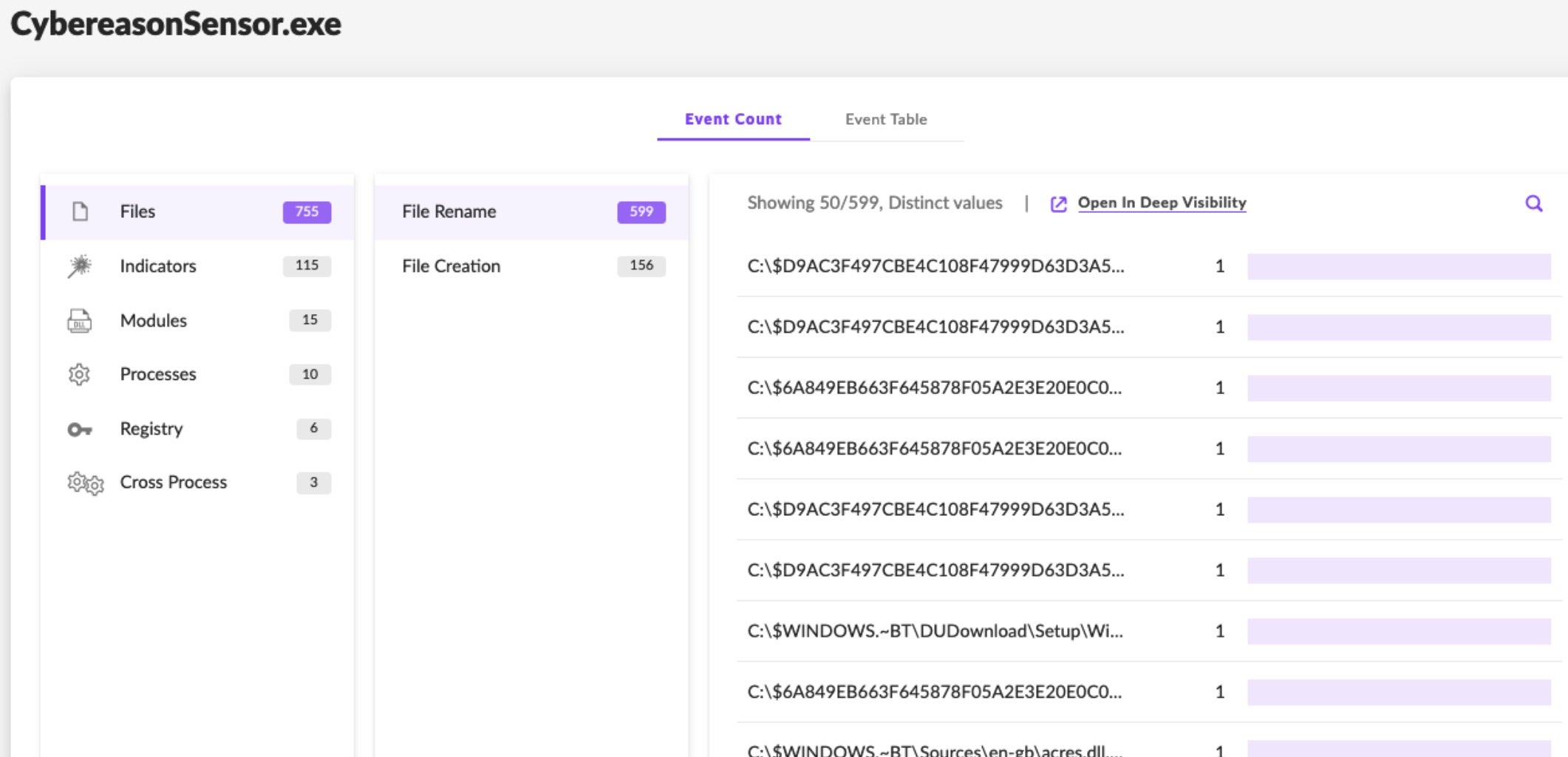
The CrossLock payload encryption relies on standard GoLang packages, working through a combination of ChaCha20 and Curve25519 (ECC). The ransomware will attempt to stop specific services or processes which may inhibit the encryption process. This varies slightly across samples. Further, the ransomware will exclude specific file names and extensions so as not to corrupt the core OS, or its own processes and artifacts.
Standard excluded file names include ntuserl.dat, desktop.ini, pagefile.sys, swapfile.sys, bootmg, bootnxt, dumpstack.log, dumpstack.log.tmp. Standard excluded extensions include .dll, .exe, .sys, .html, .htm, .bak, .lnk, .bat, .cmd
Commands supported by CrossLock include:
| Argument | Function |
| -P or -path | Specified path to encrypt |
| -H or -host | Remote host (DNS name or IP Address) to target |
| -d or -domain | Domain name (if non-default) to target |
| -ub or -uac | Toggle UAC Bypass (default is disabled) |
| -p or -pwd | Authentication Password (where required) |
| -u or -user | Specifies user (where required) . -u and -p can be used in conjunction with -H or -d |
If the threat actor omits the use of command-line arguments, the payload will simply attempt to encrypt the local device including all available volumes and files.
Upon infection, users are instructed to contact the attacker via TOX Messenger for further instructions. Affected files are given the “.lock” extension. The ransom notes, “-CrossLock_readme_to_Decrypt-.txt”, or very similar are written to each folder containing the encrypted files.
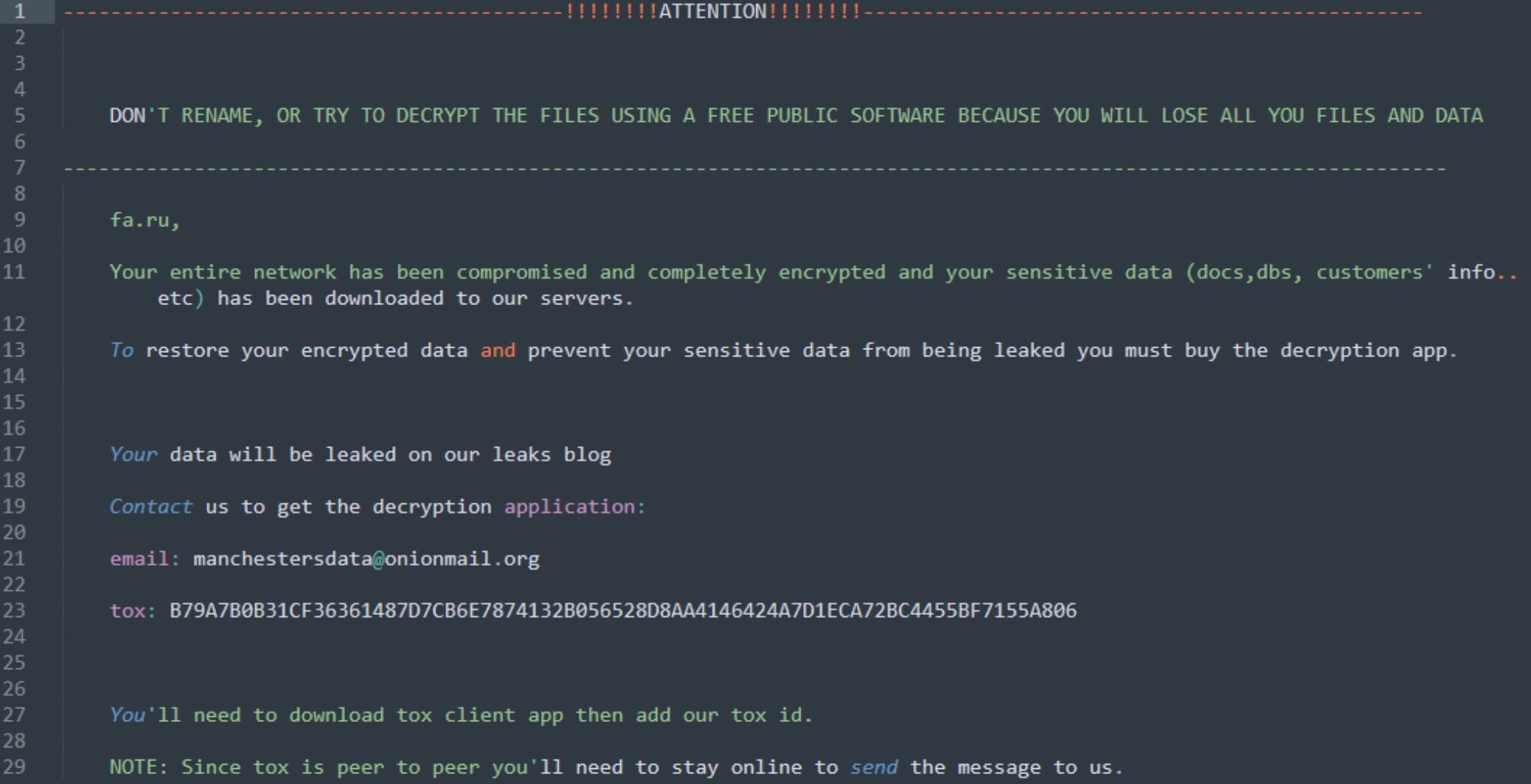
CrossLock will also attempt to inhibit the recovery of infected systems by removing Volume Shadow Copies (VSS) along with clearing Windows Event Logs (wevtutil.exe) and deleting System Backup States via wbaddmain.exe. System recovery is disabled also via bcdedit.exe.
How to Detect CrossLock Ransomware
The SentinelOne Singularity XDR Platform can identify and stop any malicious activities and items related to CrossLock ransomware.
In case you do not have SentinelOne deployed, detecting CrossLock ransomware requires a combination of technical and operational measures designed to identify and flag suspicious activity on the network. This allows the organization to take appropriate action, and to prevent or mitigate the impact of the ransomware attack.
To detect CrossLock ransomware without SentinelOne deployed, it is important to take a multi-layered approach, which includes the following steps:
- Use anti-malware software or other security tools capable of detecting and blocking known ransomware variants. These tools may use signatures, heuristics, or machine learning algorithms, to identify and block suspicious files or activities.
- Monitor network traffic and look for indicators of compromise, such as unusual network traffic patterns or communication with known command-and-control servers.
- Conduct regular security audits and assessments to identify network and system vulnerabilities and ensure that all security controls are in place and functioning properly.
- Educate and train employees on cybersecurity best practices, including identifying and reporting suspicious emails or other threats.
- Implement a robust backup and recovery plan to ensure that the organization has a copy of its data and can restore it in case of an attack.
How to Mitigate CrossLock Ransomware
The SentinelOne Singularity XDR Platform can return systems to their original state using either the Quarantine or Repair.
In case you do not have SentinelOne deployed, there are several steps that organizations can take to mitigate the risk of CrossLock ransomware attacks:
- Educate employees: Employees should be educated on the risks of ransomware, and on how to identify and avoid phishing emails, malicious attachments, and other threats. They should be encouraged to report suspicious emails or attachments, and to avoid opening them, or clicking on links or buttons in them.
- Implement strong passwords: Organizations should implement strong, unique passwords for all user accounts, and should regularly update and rotate these passwords. Passwords should be at least 8 characters long, and should include a combination of uppercase and lowercase letters, numbers, and special characters.
- Enable multi-factor authentication: Organizations should enable multi-factor authentication (MFA) for all user accounts, to provide an additional layer of security. This can be done through the use of mobile apps, such as Google Authenticator or Microsoft Authenticator, or through the use of physical tokens or smart cards.
- Update and patch systems: Organizations should regularly update and patch their systems, to fix any known vulnerabilities, and to prevent attackers from exploiting them. This includes updating the operating system, applications, and firmware on all devices, as well as disabling any unnecessary or unused services or protocols.
- Implement backup and disaster recovery: Organizations should implement regular backup and disaster recovery (BDR) processes, to ensure that they can recover from ransomware attacks, or other disasters. This includes creating regular backups of all data and systems, and storing these backups in a secure, offsite location. The backups should be tested regularly, to ensure that they are working, and that they can be restored quickly and easily.
CrossLock Ransomware FAQs
What is CrossLock ransomware?
CrossLock ransomware is a destructive malware that encrypts your files and demands cryptocurrency payment. When CrossLock infects a system, it will delete shadow copies and disable recovery options. You can recognize it by its distinctive ransom note. If you fail to pay, they will threaten to leak your data publicly.
What industries or regions are primarily targeted by CrossLock ransomware?
CrossLock primarily targets healthcare and manufacturing companies in North America and Europe. They will focus on businesses that cannot tolerate downtime. If you work in these sectors, you should implement additional security. You can see higher attack rates in regions with less cybersecurity regulation. Before you dismiss trends, check your specific risk profile.
What encryption methods does CrossLock ransomware use?
CrossLock uses AES-256 encryption for files and RSA-4096 for encryption keys. They will implement a hybrid approach making decryption without keys impossible. You can identify this through encryption speed and file patterns. If you have to analyze encrypted files, look for CrossLock’s distinctive markers. You should know breaking these methods isn’t feasible.
What file extensions are appended to files encrypted by CrossLock?
CrossLock appends “.crlck” or “.crosslock” extensions to encrypted files. They will sometimes use victim-specific extensions based on unique identifiers. You can identify affected files easily through these extensions. If you have to recover files, sorting by extensions helps determine scope. You should document all variations during incident response.
How does CrossLock ransomware gain initial access to a network?
CrossLock gains access through phishing emails with malicious attachments and exploiting unpatched VPN vulnerabilities. They will use stolen credentials to log into exposed RDP services. You can prevent access by blocking suspicious emails. If you have to secure your network, focus on these entry points. Before you ignore alerts, check these vectors.
Does CrossLock ransomware affect Windows, Linux, or both?
CrossLock affects both Windows and Linux with different variants. They will target server environments regardless of operating system. You can find Windows versions targeting workstations more frequently. If you have Linux servers, they’re vulnerable to CrossLock’s file-sharing service attacks. You should implement protection measures for both environments.
What are the indicators of compromise (IOCs) for CrossLock ransomware?
CrossLock IOCs include abnormal network traffic and file modifications with specific hash values. They will create distinctive registry keys for persistence. You can detect unusual PowerShell commands that disable security. If you have monitoring tools, look for mass file changes and encryption processes. You should watch for deletion of shadow copies.
How can organizations detect a CrossLock ransomware infection early?
You can detect CrossLock early by monitoring for unauthorized encryption processes and file system activities. They will first disable security services, so watch for those alerts. If you have network monitoring, check for command-and-control communications. You should deploy honeypot files that trigger alerts when accessed.
What preventative measures can help defend against CrossLock ransomware?
You can defend against CrossLock by implementing application whitelisting and restricting admin privileges. They will try to exploit outdated systems, so patch regularly. If you have security tools, configure them to block known indicators. You should segment your network to limit lateral movement. Before connecting devices, verify their security.
What should be done immediately after a CrossLock ransomware infection?
If you discover a CrossLock infection, immediately isolate affected systems from the network. They will try to spread if connections remain. You can preserve evidence by creating system images before remediation. If you have incident response plans, activate them right away. You should contact law enforcement and report the attack.