Good Day Ransomware: In-Depth Analysis, Detection, and Mitigation
What Is Good Day Ransomware?
Good Day ransomware was first observed in May of 2023 and is a variant of the ARCrypter family. This variant’s name is based on the message displayed to victims upon visiting the threat actor’s victim portal; a TOR-based website.
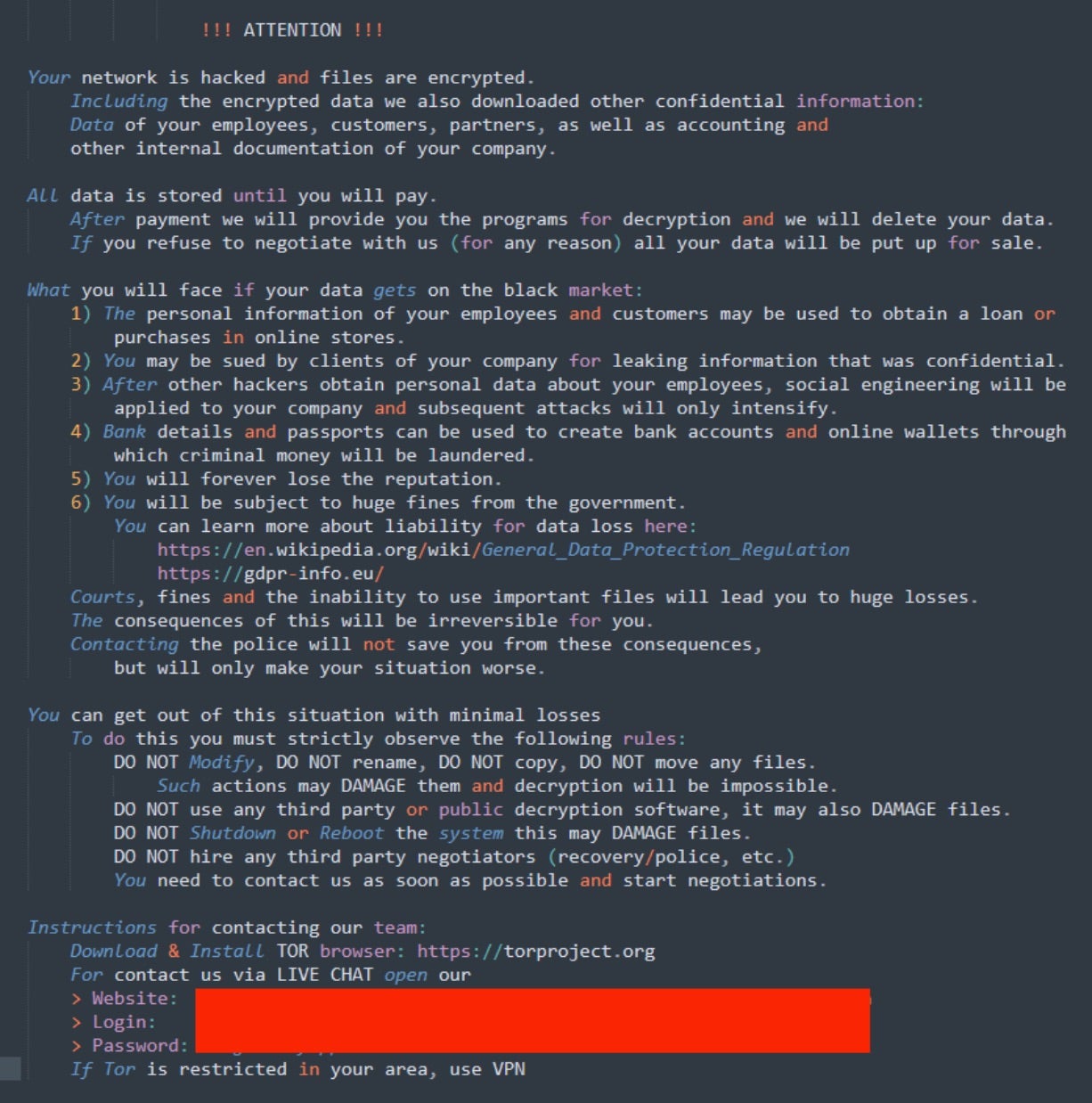
ARCrypter has been associated with notable attacks against the Chilean government. Other variants include ChileLocker and REDALERT ransomware. Currently, there is no public victim blog or website associated with Good Day ransomware. Victims are, however, required to engage the threat actor via the TOR-based portal for instructions on how to recover their data.

What Does Good Day Ransomware Target?
Good Day, and its predecessors, have been associated with attacks against Chilean government facilities and those within a similar periphery.
How Does Good Day Ransomware Work?
Good Day is a member of the ARCrypter family. Good Day ransomware payloads masquerade as valid updates for the Windows OS (e.g., n211p1a1hs1_win_x64_v1a.exe). Initial delivery methods of Good Day payloads is a phishing email with links to the masqueraded payload.
When launched, Good Day will query for the infected host’s location via HKEY_USERS…\Control Panel\International\Geo\Nation
Persistence is achieved via an entry in the RUN key of the registry:
Example: cmd.exe /c reg add hklm\Software\Microsoft\Windows\CurrentVersion\Run /v SecurityUpdate /t REG_EXPAND_SZ /d C:\Users\admin1\AppData\Local\Temp\489B6B.exe /f
The ransomware will also attempt to remove VSS (Volume Shadow Copies) via VSSADMIN.EXE
Example: cmd.exe (vssadmin.exe) /c vssadmin.exe delete shadows /all /quiet
The ransomware queries the infected systems via WMIC query.
Example: start iwbemservices::execquery - root\cimv2 : select __path, processid, csname, caption, sessionid, threadcount, workingsetsize, kernelmodetime, usermodetime from win32_process
The ransomware renames encrypted files with the .crYpt extension.
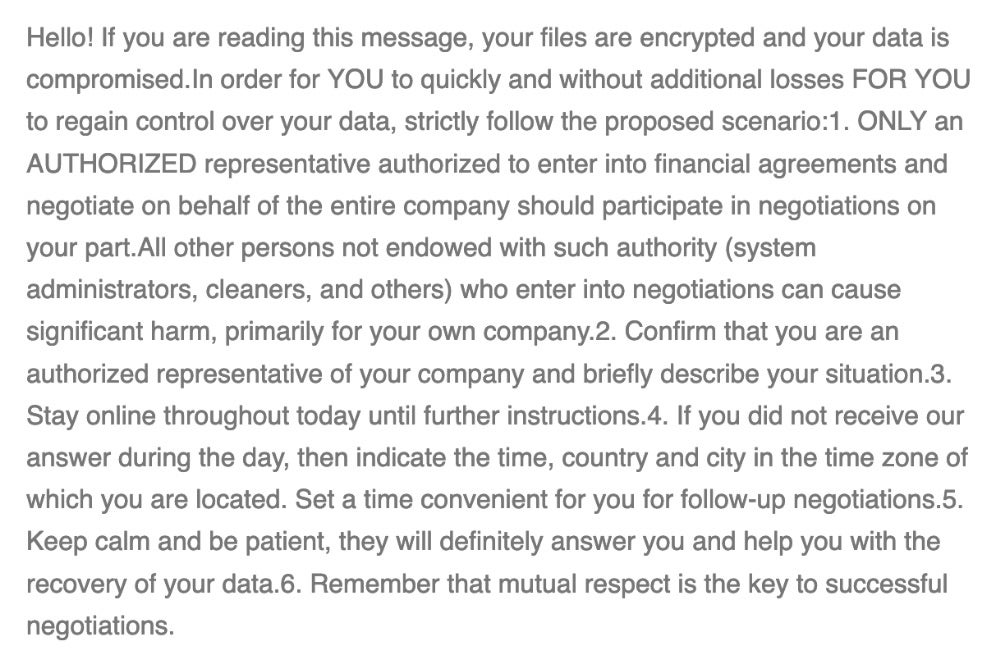
The Good Day ransomware notes are written as readme_for_unlock.txt
How to Detect Good Day Ransomware
The SentinelOne Singularity XDR Platform can identify and stop any malicious activities and items related to Good Day ransomware.
In case you do not have SentinelOne deployed, detecting Good Day ransomware requires a combination of technical and operational measures designed to identify and flag suspicious activity on the network. This allows the organization to take appropriate action, and to prevent or mitigate the impact of the ransomware attack.
To detect Good Day ransomware without SentinelOne deployed, it is important to take a multi-layered approach, which includes the following steps:
- Use anti-malware software or other security tools capable of detecting and blocking known ransomware variants. These tools may use signatures, heuristics, or machine learning algorithms, to identify and block suspicious files or activities.
- Monitor network traffic and look for indicators of compromise, such as unusual network traffic patterns or communication with known command-and-control servers.
- Conduct regular security audits and assessments to identify network and system vulnerabilities and ensure that all security controls are in place and functioning properly.
- Educate and train employees on cybersecurity best practices, including identifying and reporting suspicious emails or other threats.
- Implement a robust backup and recovery plan to ensure that the organization has a copy of its data and can restore it in case of an attack.
How to Mitigate Good Day Ransomware
The SentinelOne Singularity XDR Platform can return systems to their original state using either the Repair or Rollback feature.
In case you do not have SentinelOne deployed, there are several steps that organizations can take to mitigate the risk of Good Day ransomware attacks:
- Educate employees: Employees should be educated on the risks of ransomware, and on how to identify and avoid phishing emails, malicious attachments, and other threats. They should be encouraged to report suspicious emails or attachments, and to avoid opening them, or clicking on links or buttons in them.
- Implement strong passwords: Organizations should implement strong, unique passwords for all user accounts, and should regularly update and rotate these passwords. Passwords should be at least 8 characters long, and should include a combination of uppercase and lowercase letters, numbers, and special characters.
- Enable multi-factor authentication: Organizations should enable multi-factor authentication (MFA) for all user accounts, to provide an additional layer of security. This can be done through the use of mobile apps, such as Google Authenticator or Microsoft Authenticator, or through the use of physical tokens or smart cards.
- Update and patch systems: Organizations should regularly update and patch their systems, to fix any known vulnerabilities, and to prevent attackers from exploiting them. This includes updating the operating system, applications, and firmware on all devices, as well as disabling any unnecessary or unused services or protocols.
- Implement backup and disaster recovery: Organizations should implement regular backup and disaster recovery (BDR) processes, to ensure that they can recover from ransomware attacks, or other disasters. This includes creating regular backups of all data and systems, and storing these backups in a secure, offsite location. The backups should be tested regularly, to ensure that they are working, and that they can be restored quickly and easily.
Rook Ransomware FAQs
What is Good Day ransomware?
The Good Day ransomware is a member of the ARCrypter family and was first observed in May 2023. It has launched attacks on the Chilean government and communicates with its victims via a TOR-based portal, where it sends them instructions on how to recover their data after they’ve been infected.
How does Good Day ransomware encrypt files?
Good Day ransomware payloads masquerade as valid updates for the Windows OS (e.g., n211p1a1hs1_win_x64_v1a.exe). The initial delivery method of Good Day payloads is a phishing email with links to the masqueraded payload.
When launched, Good Day will query for the infected host’s location via HKEY_USERS…\Control Panel\International\Geo\Nation.
The ransomware will also attempt to remove VSS (Volume Shadow Copies) via VSSADMIN.EXE.
Example: cmd.exe (vssadmin.exe) /c vssadmin.exe delete shadows /all /quiet
The ransomware queries the infected systems via a WMIC query.
Example: start iwbemservices::execquery – root\cimv2: select __path, processid, csname, caption, sessionid, threadcount, workingsetsize, kernelmodetime, usermodetime from win32_process
The ransomware renames encrypted files with the .crYpt extension.
How can organisations detect Good Day ransomware?
You will find Good Day ransomware notes written as readme_for_unlock.txt files. Organisations can detect Good Day ransomware by using the SentinelOne Singularity XDR Platform. If they don’t have SentinelOne, they can use anti-malware solutions, security audits, and a mix of other security tools and AI threat detection solutions to detect it.
What preventive measures can be taken against Good Day ransomware?
This should be obvious, but regularly backing up your data and implementing proactive security monitoring is a first step. Enable multi-factor authentication, create strong passwords, and teach your employees to identify and spot ransomware’s invasion attempts.
Are there specific tools recommended for detecting Good Day ransomware?
Yes. SentinelOne Singularity XDR Platform can be used for detecting Good Day ransomware strains. It can automatically detect and block its malicious processes and prevent future attacks.
What steps should be taken if infected by Good Day ransomware?
If you think the Good Day ransomware has infected you and your organisation is in trouble, here’s what you can do:
- Isolate infected systems and quarantine the infection immediately. Disconnect connected devices from the network to prevent further spread. You can take your whole network offline, and that’s a good move.
- Don’t forget to report to the Cybersecurity and Infrastructure Security Agency (CISA) and the FBI’s Internet Crime Complaint Center (IC3). Once your network is offline and you think the infection has been contained, you can recover using previously verified backups.
- Don’t pay the ransom or cave into demands, no matter what. Apply the latest patches and software updates and strengthen your cybersecurity posture by implementing MFA, ZTNA, and least privilege access.