TellYouThePass Ransomware: In-Depth Analysis, Detection, and Mitigation
What Is TellYouThePass Ransomware?
TellYouThePass is a commodity-level ransomware that emerged in 2019. This ransomware family saw a resurgence in parallel with recent exploitation of Apache (Log4j) vulnerabilities. Currently, TellYouThePass ransomware does not host a public blog nor a repository of victims and their respective data.
What Does TellYouThePass Ransomware Target?
TellYouThePass is low-sophistication ransomware that is used to target businesses as well as private individuals. Increased targeting of specific vulnerabilities such as CVE-2021-44228 has been observed.
How Does TellYouThePass Ransomware Work?
Modern TellYouThePass ransomware payloads are written in Go. The ransomware uses a combination of AES-256 and RSA-1024 for encryption of files and has builds for both Windows and Linux operating systems. Upon execution, TellYouThePass will gather requisite system information and attempt to terminate any process (or service) that may inhibit the encryption process. The following commands are issued to terminate processes:
taskkill /f /im dbeng50.exe
taskkill /f /im dbsnmp.exe
taskkill /f /im excel.exe
taskkill /f /im firefoxconfig.exe
taskkill /f /im infopath.exe
taskkill /f /im msaccess.exe
taskkill /f /im msftesql.exe
taskkill /f /im mspub.exe
taskkill /f /im mydesktopqos.exe
taskkill /f /im mydesktopservice.exe
taskkill /f /im mysqld-nt.exe
taskkill /f /im mysqld-opt.exe
taskkill /f /im mysqld.exe
taskkill /f /im ocautoupds.exe
taskkill /f /im ocomm.exe
taskkill /f /im ocssd.exe
taskkill /f /im onenote.exe
taskkill /f /im oracle.exe
taskkill /f /im outlook.exe
taskkill /f /im powerpnt.exe
taskkill /f /im sqbcoreservice.exe
taskkill /f /im sqlagent.exe
taskkill /f /im sqlbrowser.exe
taskkill /f /im sqlservr.exe
taskkill /f /im sqlwriter.exe
taskkill /f /im steam.exe
taskkill /f /im synctime.exe
taskkill /f /im tbirdconfig.exe
taskkill /f /im thebat.exe
taskkill /f /im thebat64.exe
taskkill /f /im thunderbird.exe
taskkill /f /im tnslsnr.exe
taskkill /f /im visio.exe
taskkill /f /im winword.exe
taskkill /f /im wordpad.exe
taskkill /f /im xfssvccon.exe
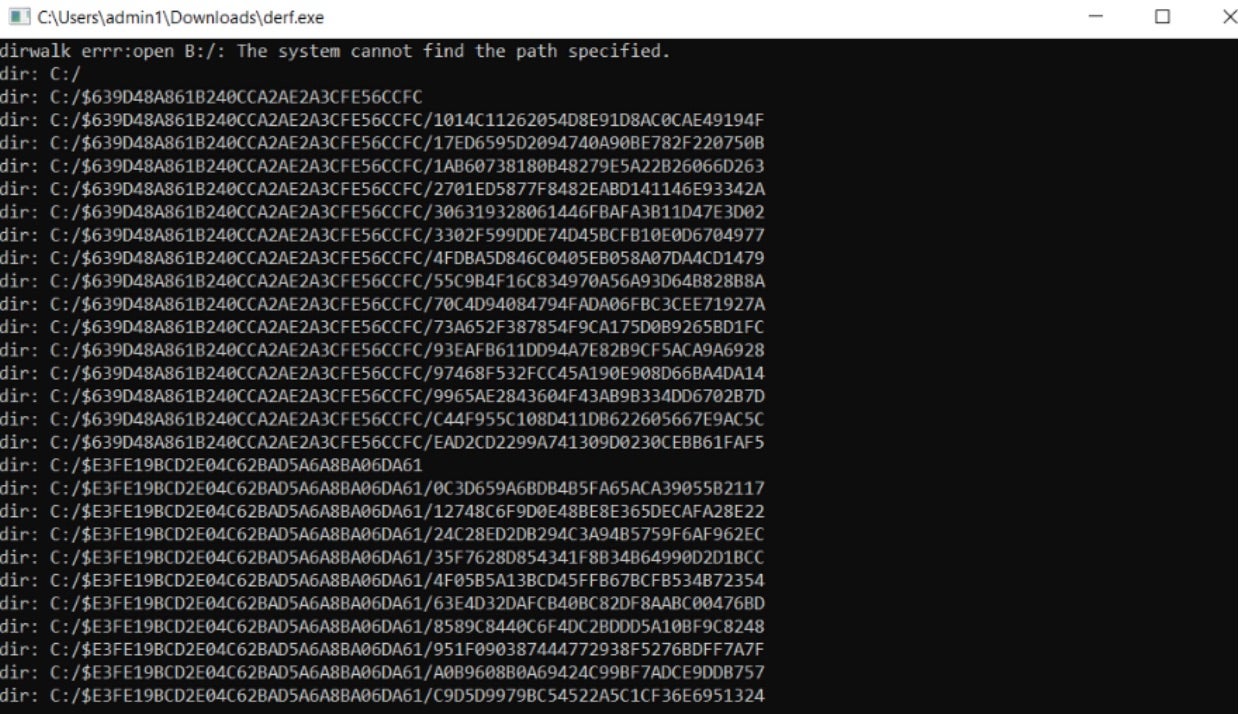
TellYouThePass execution is very visible on infected hosts with visible command windows displaying the status of the encryption process.
TellYouThePass ransomware will then enumerate local drives, alphabetically, in order of drive letter and encrypt files. Affected files will be appended with the .LOCKED extension.
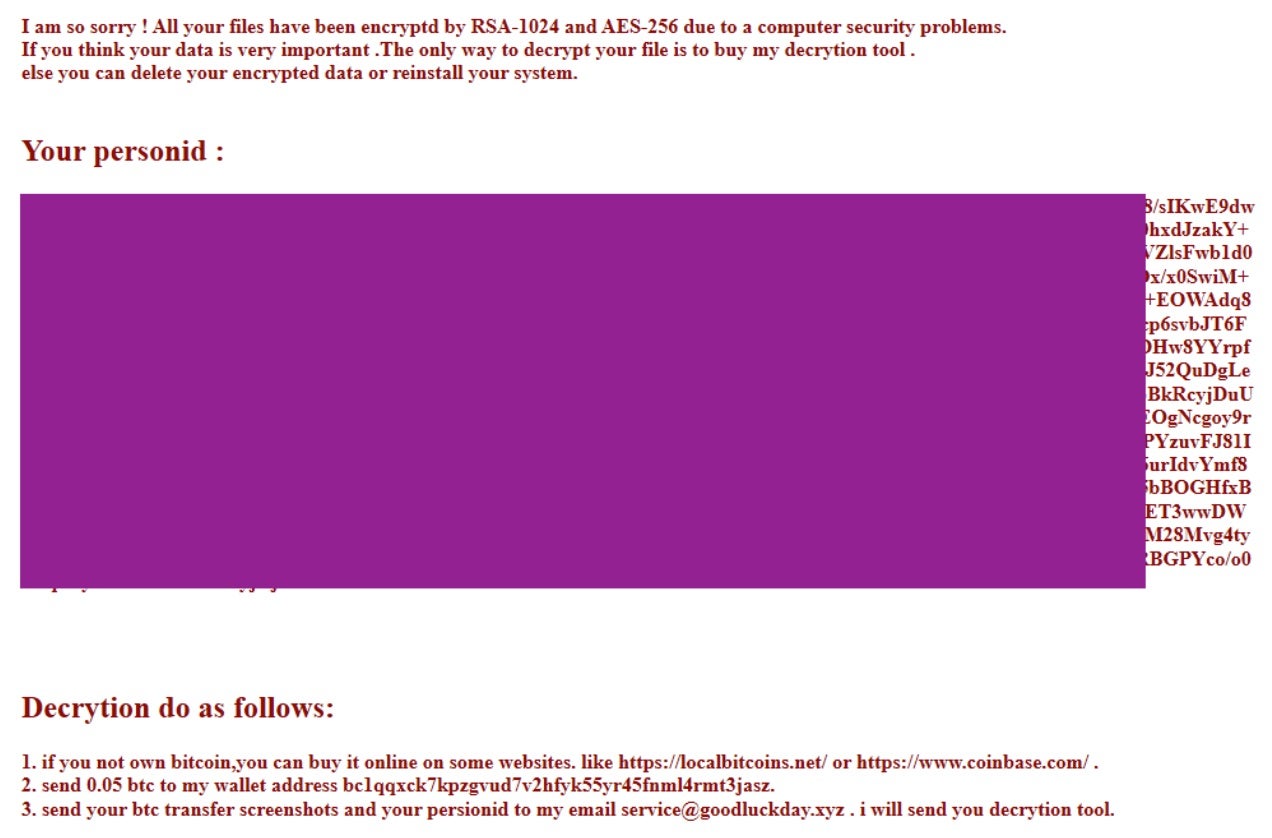
In terms of ransom notes, TellYouThePass demands are written to each affected directory as README.HTML. Victims of TellYouToPass are instructed to pay via Bitcoin to a specific crypto wallet address. Once that step is completed, the victim is to submit proof of payment and various identifiers to the attacker via email.
How to Detect TellYouThePass Ransomware
The SentinelOne Singularity XDR Platform can identify and stop any malicious activities and items related to TellYouThePass ransomware.
In case you do not have SentinelOne deployed, detecting TellYouThePass ransomware requires a combination of technical and operational measures designed to identify and flag suspicious activity on the network. This allows the organization to take appropriate action, and to prevent or mitigate the impact of the ransomware attack.
To detect TellYouThePass ransomware without SentinelOne deployed, it is important to take a multi-layered approach, which includes the following steps:
- Use anti-malware software or other security tools capable of detecting and blocking known ransomware variants. These tools may use signatures, heuristics, or machine learning algorithms, to identify and block suspicious files or activities.
- Monitor network traffic and look for indicators of compromise, such as unusual network traffic patterns or communication with known command-and-control servers.
- Conduct regular security audits and assessments to identify network and system vulnerabilities and ensure that all security controls are in place and functioning properly.
- Educate and train employees on cybersecurity best practices, including identifying and reporting suspicious emails or other threats.
- Implement a robust backup and recovery plan to ensure that the organization has a copy of its data and can restore it in case of an attack.
How to Mitigate TellYouThePass Ransomware
The SentinelOne Singularity XDR Platform can return systems to their original state using either the Repair or Rollback feature.
In case you do not have SentinelOne deployed, there are several steps that organizations can take to mitigate the risk of TellYouThePass ransomware attacks:
- Educate employees: Employees should be educated on the risks of ransomware, and on how to identify and avoid phishing emails, malicious attachments, and other threats. They should be encouraged to report suspicious emails or attachments, and to avoid opening them, or clicking on links or buttons in them.
- Implement strong passwords: Organizations should implement strong, unique passwords for all user accounts, and should regularly update and rotate these passwords. Passwords should be at least 8 characters long, and should include a combination of uppercase and lowercase letters, numbers, and special characters.
- Enable multi-factor authentication: Organizations should enable multi-factor authentication (MFA) for all user accounts, to provide an additional layer of security. This can be done through the use of mobile apps, such as Google Authenticator or Microsoft Authenticator, or through the use of physical tokens or smart cards.
- Update and patch systems: Organizations should regularly update and patch their systems, to fix any known vulnerabilities, and to prevent attackers from exploiting them. This includes updating the operating system, applications, and firmware on all devices, as well as disabling any unnecessary or unused services or protocols.
- Implement backup and disaster recovery: Organizations should implement regular backup and disaster recovery (BDR) processes, to ensure that they can recover from ransomware attacks, or other disasters. This includes creating regular backups of all data and systems, and storing these backups in a secure, offsite location. The backups should be tested regularly, to ensure that they are working, and that they can be restored quickly and easily.
TellYouThePass Ransomware FAQs
What is TellYouThePass ransomware?
TellYouThePass is a ransomware family first seen in 2019. The attackers encrypt files and demand payment for decryption. They leave ransom notes named “DECRYPT_INFORMATION.txt” with contact details. The ransomware deletes shadow copies to prevent easy recovery. Once it finishes encryption, files will have the .tltp extension added.
Which operating systems are targeted by TellYouThePass ransomware?
TellYouThePass mainly targets Windows systems from 7 through 11 and attacks Windows Server environments. Newer versions also target Linux systems, especially web servers. The ransomware checks the OS version before starting encryption. It attacks both 32-bit and 64-bit systems across multiple platforms.
What encryption algorithms does TellYouThePass ransomware use?
TellYouThePass uses AES-256 and RSA-4096 for encryption. It will create unique keys for each infected system. The ransomware will encrypt local keys with a public key controlled by attackers. Files will be locked with strong ciphers, making recovery impossible without the key. You can’t break this encryption with current technology.
How does TellYouThePass ransomware propagate within networks?
TellYouThePass will exploit unpatched systems. It will move through SMB shares between computers. The ransomware will scan for open RDP ports and try brute force attacks. They will deploy it using stolen credentials and move sideways through networks. If you have mapped drives, it will also spread to those locations.
What are common indicators of a TellYouThePass ransomware infection?
You can spot TellYouThePass by ransom notes in encrypted folders. Look for files with the .tltp extension across multiple directories. The ransomware will create registry keys for persistence. It will connect to command servers in China and Russia. You might see suspicious executables with random names running if you check processes.
How can organisations detect an ongoing TellYouThePass ransomware attack?
You can catch TellYouThePass through abnormal file access patterns. Monitor for mass file changes and name alterations. Watch for unexpected PowerShell commands running. The ransomware will try to turn off security software. Network traffic will show communication with known bad IPs. If you see these signs, isolate affected systems immediately.
What is known about the group behind TellYouThePass ransomware?
The group behind TellYouThePass operates from East Asia. They demand Bitcoin payment, usually between 0.5 and 5 BTC. The attackers communicate through ProtonMail and Telegram. If ransoms aren’t paid, they sometimes leak stolen data on dark web forums. Through shared infrastructure, you can find links between them and other cybercrime groups.