The Good | DoJ Seize $8.2 Million in Cryptocurrency Linked to Romance Baiting Schemes
The DoJ has seized over $8.2 million in USDT (Tether) cryptocurrency, all stolen through ‘romance baiting’ scams, formerly known as ‘pig butchering’. Victims are manipulated into making investments on fake websites or apps after being promised substantial returns. They are then led to believe they are making profits so invest even more, only to run into a multitude of issues when trying to make any withdrawals. At this point, the scammers have already made off with all of the victim’s funds.
The FBI backward-traced the laundering patterns across multiple platforms and networks starting from centralized exchanges, then Ethereum and TRON, through DeFi protocols, and finally, into storage wallets owned by the fraudsters. Analysis on the investigation noted that U.S. state investigators were able to file a dual legal forfeiture under charges of wire fraud and money laundering.
Tether Limited cooperated by freezing the stolen funds, burning the original tokens, and reissuing them to law enforcement-controlled wallets. The asset seizure was successfully completed in November 2024, and now enables potential restitution for victims as the FBI continues to trace affected accounts.
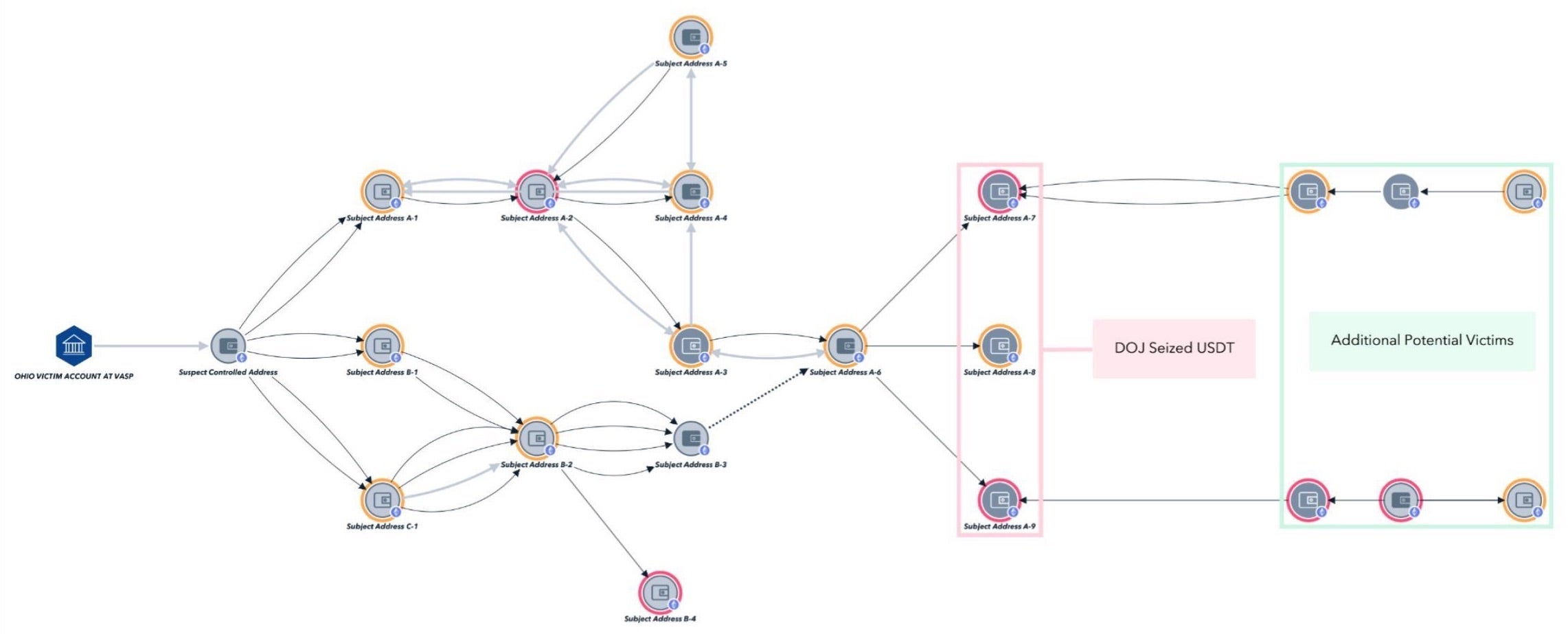
One filed complaint identifies 38 cryptocurrency accounts victimized by these scams, with total losses exceeding $5.2 million. Five named victims from Ohio, Michigan, California, Utah, and North Carolina collectively lost over $1.6 million, with the worst case involving someone liquidating their retirement account, leading to a $650,000 loss. These major seizures showcase the DOJ’s commitment to dismantling sophisticated cryptocurrency scams and ensuring justice for victims.
The Bad | China-linked Threat Actor Exploits Ivanti Bug CVE-2025-22457
A critical vulnerability in several Ivanti products is being actively exploited in the wild, with attackers using it to gain remote access, deploy malware, and establish long-term persistence in victim environments.
Tracked as CVE-2025-22457, the flaw is a stack-based buffer overflow vulnerability with a CVSS score of 9.0, affecting Ivanti’s Connect Secure, Policy Secure, and Neurons for ZTA Gateways. The bug allows remote, unauthenticated attackers to execute arbitrary code on vulnerable systems.
Ivanti says the issue stems from how the gateway handles certain limited character inputs—specifically, periods and numbers. While the flaw was initially assessed as not meeting the criteria for remote code execution or denial of service, subsequent analysis revealed that it could be exploited through sophisticated methods and evidence of active exploitation in the wild has since emerged.
A campaign abusing the vulnerability was observed in mid-March 2025 and attributed to a China-linked threat actor tracked as UNC5221. The attackers employed TRAILBLAZE, an in-memory dropper, to deliver the initial payload. Once access is established, BRUSHFIRE, a memory-resident backdoor, is injected into the web process of the Ivanti appliance, enabling remote command execution without writing to disk. To maintain persistence and expand access, the attackers leveraged a malware framework known as SPAWN, with capabilities for log tampering, memory extraction, and other post-exploitation activity.
Vulnerable edge devices attract threat actors like honey. UNC5221 (China-linked Threat Actor) has been actively exploiting CVE-2025-22457 (CVSS 9.0) a critical Ivanti VPN vulnerability since mid-March 2025. Patch version 22.7R2.6
#CVE #Exploited #POC #patch #vulnerability— Mario Rojas (@mariorojaschin.bsky.social) 3 April 2025 at 17:35
To mitigate the threat, Ivanti released a patch for Connect Secure 22.7R2.6 on February 11, 2025. Fixes for Policy Secure (22.7R1.4) and Neurons for ZTA Gateway (22.8R2.2) are scheduled for release later this month. Ivanti says that Policy Secure should not be exposed to the public internet and that Neurons for ZTA Gateway is not exploitable in production deployments.
Ivanti strongly encourages its customers to update to Connect Secure 22.7R2.6 as soon as possible. The company’s full mitigation advice can be found here.
The Ugly | New WRECKSTEEL Malware Used in Cyber Espionage Campaigns Targeting Ukraine
Ukraine’s computer emergency response team, CERT-UA, has reported at least three cyberattacks from March focused on targeting government agencies and critical infrastructure using a new malware dubbed ‘WRECKSTEEL’. This is a targeted espionage campaign now attributed to the threat cluster tracked as UAC-0219 that has been active since fall of 2024 and is known for employing phishing emails to spread malicious links.
UAC-0219: Cyber Espionage using #PowerShell #stealer #WRECKSTEEL
Details: https://t.co/dGelGv4F0y (UA only) pic.twitter.com/fEjCdf9LoN— CERT-UA (@_CERT_UA) April 3, 2025
Attackers compromised the government accounts to send messages with links to public file-sharing services such as Google Drive and DropMeFiles. In one phishing attempt, the attackers masqueraded as a Ukrainian government agency, sending out fake salary reduction notices to lure employees into clicking malicious links. Clicking the links triggered the download of a Visual Basic Script (VBS) loader, which then executed a PowerShell script designed to collect documents, images, PDFs, and presentations with specific extensions to capture screenshots.
While early versions of UAC-0219 relied on EXE files, VBS stealers, and the IrfanView image editor for data extraction, the integration of the screenshot functionality directly into the PowerShell script to perform espionage confirms the continued development of the malware.
While CERT-UA did not directly attribute the attacks to a nation, similar phishing campaigns have historically originated from Russia. The attacks reflect increasing sophistication, using PowerShell-based techniques to bypass detection and collect targeted data. CERT-UA released a full list of IoCs to help organizations detect and mitigate these threats.


