The Good | Leaders of Crypto Investment Scam Arrested & Charged for $73 Million Laundering Scheme
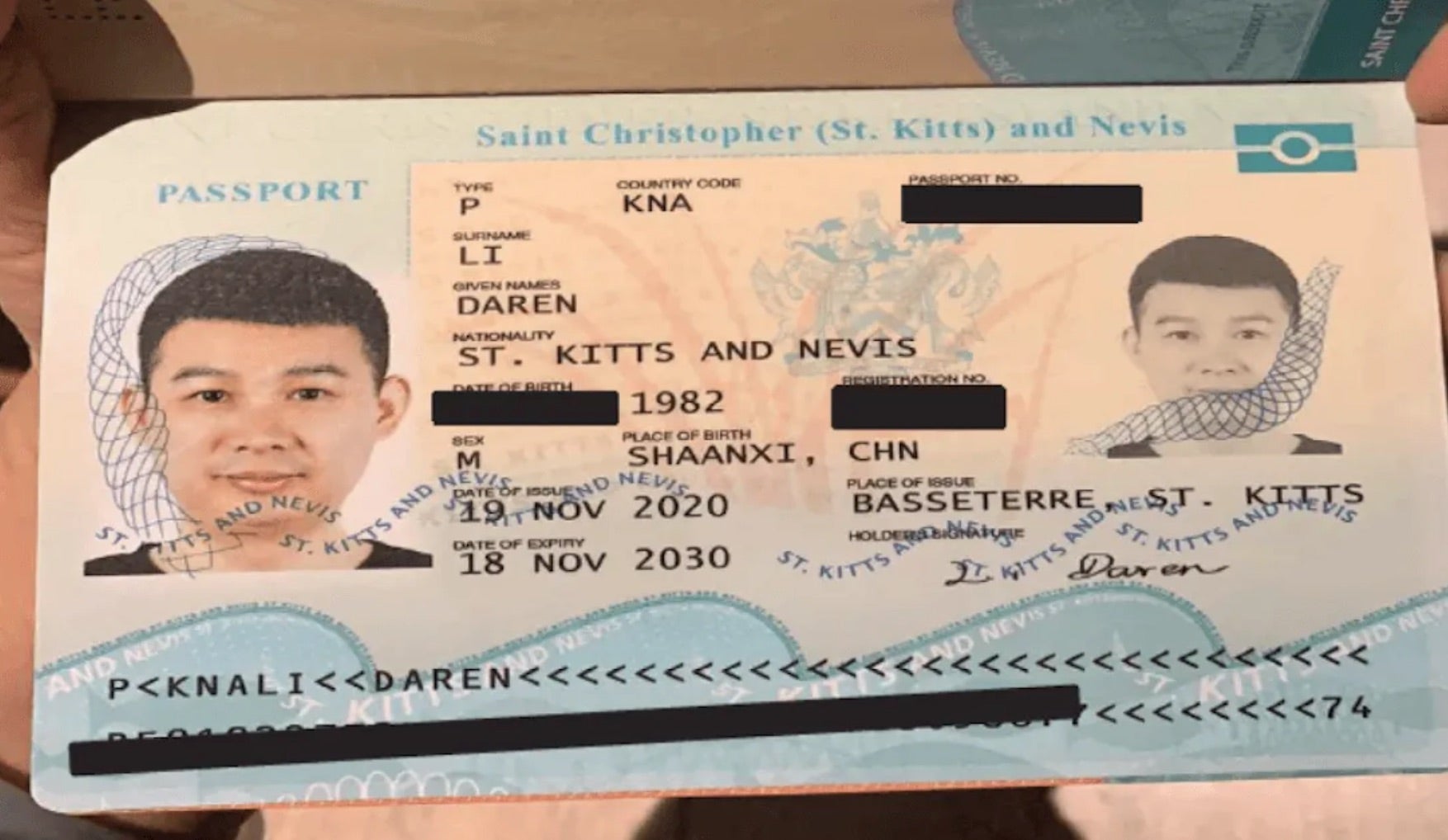
This week, the tables were turned on two alleged cyber ‘pig butcherers’ who could now face time in the iron pen. The DoJ indicted Daren Li (41) and Yicheng Zhang (38) for their alleged roles leading a global syndicate that has laundered over $73 million through cryptocurrency investment scams. Both Li and Zhang are charged with conspiracy to commit money laundering and six counts of international laundering. If convicted, they face 20 years in prison on each count.
Pig butchering scams involve criminals building up trust with targeted victims via social media and messaging or dating platforms to convince them to invest in fraudulent schemes. After falling for the bait, the criminals then steal their victims’ cryptocurrency, draining the compromised wallets.
According to court documents, Li and Zhang transferred millions of their victims’ cryptocurrency to U.S. bank accounts connected to shell companies. The funds were then moved through various domestic and international accounts and crypto platforms in order to obscure their origins. Communications uncovered during the investigation revealed details on the operations, including commissions, victim information, and interactions with U.S. financial institutions.
In 2023 alone, the U.S. Secret Service recovered more than $1.1 billion from scam operations and the IC3 reported that investment fraud investment scams rose from $3.31 billion in 2022 to $4.57 billion last year. As schemes revolving around financial fraud become increasingly common and complex, cyber defenders reiterate the importance of learning how to spot predatory behavior online, staying vigilant with securing digital assets and identities, verifying the legitimacy of brokerages before investing, and reporting suspicions of fraud immediately.
The Bad | Threat Actors Exploit Legitimate Cloud Services to Deliver Malware in Emerging Campaign
In a new attack campaign, popular cloud storage services like Google Drive and Dropbox are being exploited to stage malicious payloads. Dubbed “CLOUD#REVERSER”, security researchers this week broke down how the campaign uses VBScript and PowerShell to perform command and control-like (C2) activities within the storage platforms to manage file uploads and download.
Attacks begin with a phishing email containing a ZIP archive file that includes an executable disguised as a Microsoft Excel file. This is done through making use of the hidden right-to-left override (RLO) Unicode character (U+202E) so that the order of the characters in the string are reserved. In this case, the victims receiving the email would see the file name RFQ-101432620247fl*U+202E*xslx.exe as RFQ-101432620247flexe.xlsx and open the file thinking it is a legitimate Excel spreadsheet. This is not a new trick, but it is less commonly seen in 2024.
Executing this file drops a total of eight payloads, one of which includes a decoy Excel file and an obfuscated VBScript that displays the .xlsx file to continue the deception. From there, a series of additional scripts allow the threat actor to establish persistence on the system, connect to the actor-controlled Google Drive and Dropbox accounts, fetch files from the storage services, and maintain connection to the actor’s command and control (C2) server.
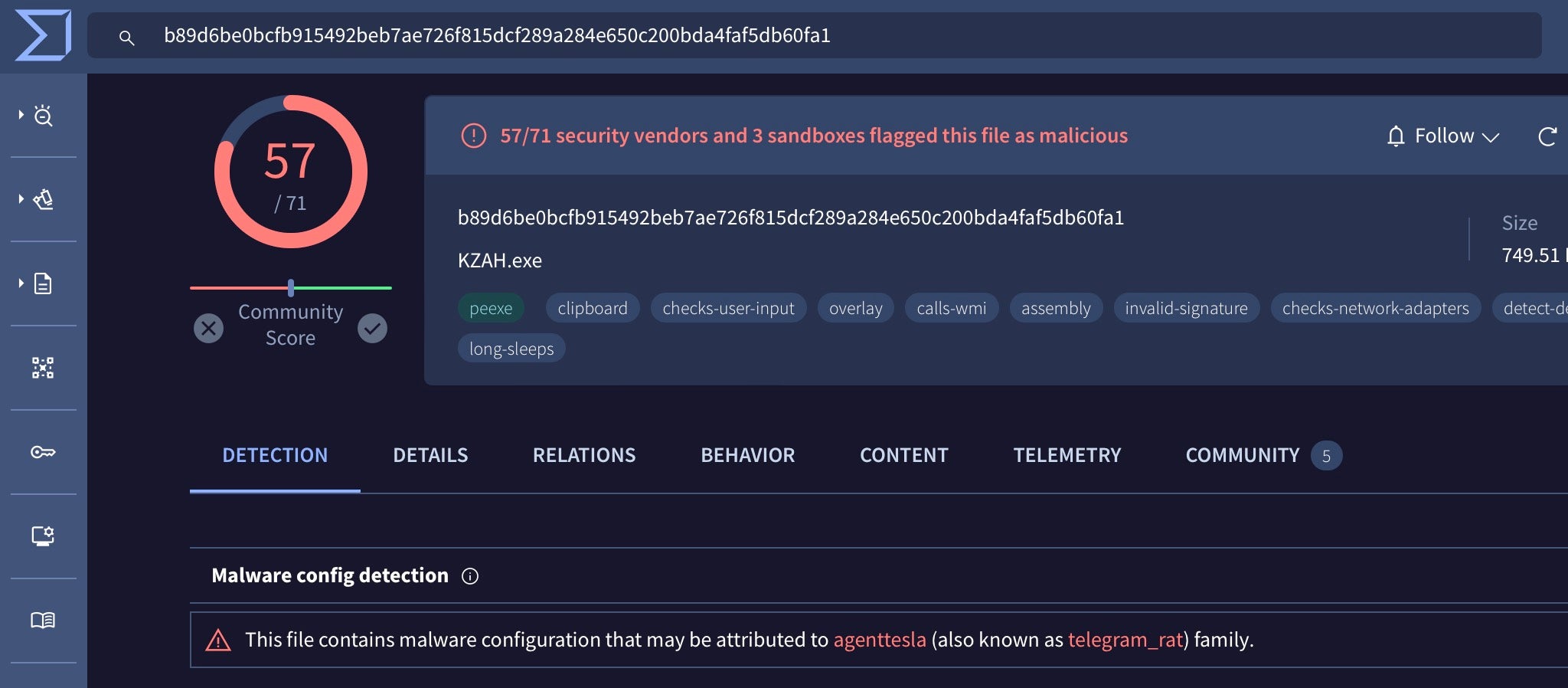
These developing attacks highlight the trend of threat actors abusing SaaS platforms to deliver malicious payloads under the guise of legitimate network traffic. By embedding multi-stage downloaders that run code within widely-used cloud platforms, the threat actors can ensure they have persistent access for data exfiltration while keeping a low profile.
The Ugly | Military & Government Orgs Repeatedly Targeted by New PRC-Linked Threat Actor Over 6 Years
Details on a previously undocumented threat group called “Unfading Sea Haze” emerged this week when cybersecurity researchers reported on a series of attacks across countries bordering the South China Sea. So far, eight high-level organizations in critical sectors have been repeatedly targeted over the last six years with the attackers’ exploiting poor credential hygiene and unpatched devices and web services in particular.
New APT Group “Unfading Sea Haze” Hits Military Targets in South China Sea https://t.co/XHNQPc1ccz
— Nicolas Krassas (@Dinosn) May 23, 2024
Unfading Sea Haze is currently not linked to any known APT group, but appears to share similar goals, techniques, geopolitical victimology, and choice of tools known to be associated with Chinese-speaking threat actors. This includes the use of Gh0st RAT malware and running a tool called SharpJHandler, often employed by PRC-based APT41.
So far, Unfading Sea Haze has been observed sending spear phishing emails containing Windows shortcut (LNK) files. When launched, these files execute commands to retrieve the next-stage payload, a backdoor called “SerialPktdoor”, which then runs PowerShell scripts and manages files remotely. Also characteristic of Unfading Sea Haze attacks is use the Microsoft Build Engine (MSBuild) to execute files filelessly and minimize the risk of detection, and scheduled tasks to load a malicious DLL and establish persistence.
Other tools in the group’s arsenal include “Ps2dllLoader”, keylogger called “xkeylog”, a web browser data stealer, a monitoring tool keyed to the presence of portable devices, and a custom data exfiltration program named “DustyExfilTool”. The widely varied and complex toolkit points to a certain level of sophistication. Researchers note that the combination of both custom and commercial tools is indicative of a cyber espionage campaign, aimed at gathering sensitive information from military and government entities.
Organizations can mitigate the risks threat groups like Unfading Sea Haze pose with the SentinelOne Singularity platform.
Good security hygiene such as timely patch management, strong authentication methods, and secure credentials is also highly recommended.



