A recent wave of Twitter/X account takeover attacks has seen multiple high-profile social media accounts compromised and used to spread malicious content aimed at stealing cryptocurrency. The attacks use a family of malware known as crypto-drainers and often supplied through Drainer-as-a-Service (DaaS) platforms. Some recent high-profile victims include the SEC and Mandiant.
Crypto Drainers and Drainers as a Service have received little attention from security researchers to date despite having been around since at least 2021. In this post, we turn the spotlight on Crypto Drainers and DaaS to raise awareness of this family of threats and how it impacts organizations.

Introduction to DaaS and Crypto Drainers
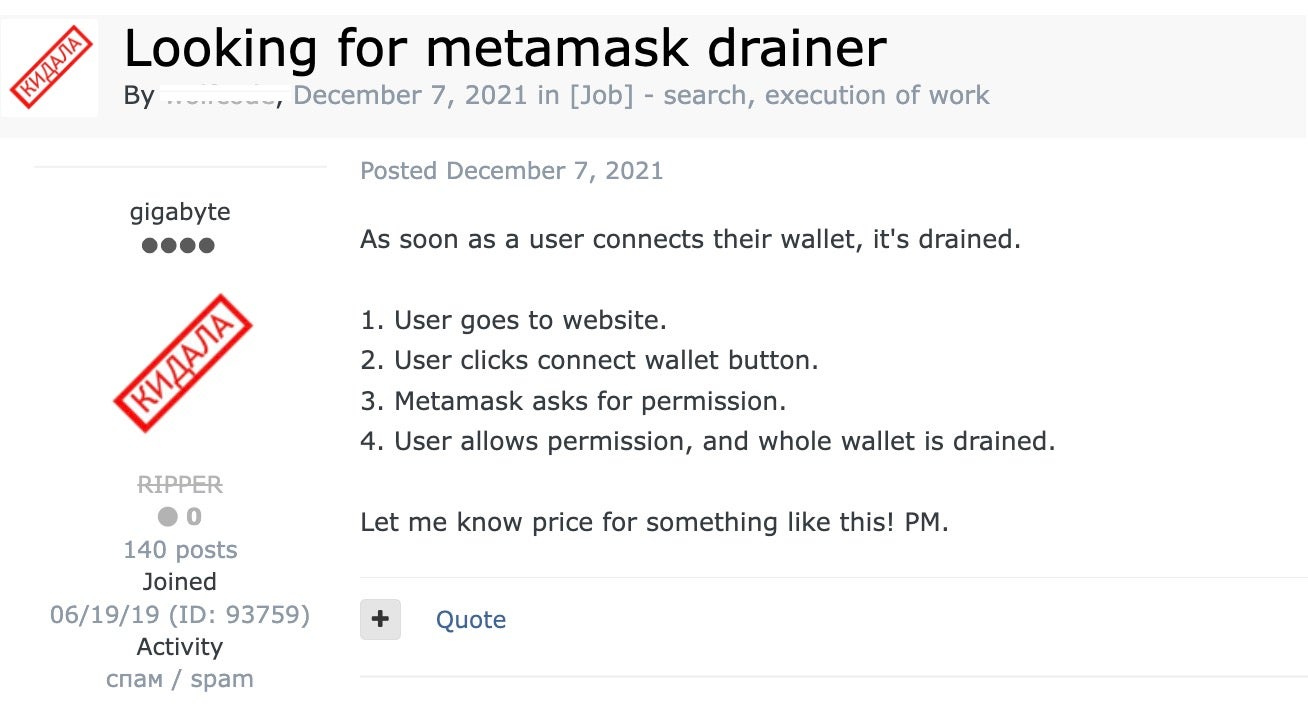
A crypto drainer is a malicious tool or script that is specially designed to transfer or redirect cryptocurrency from a victim’s wallet to that under the control of an attacker. Drainers targeting MetaMask first appeared around 2021, where they were openly marketed in underground forums and marketplaces.
However, drainers and drainer-style attacks can exist in several forms. Malicious smart contracts may contain hidden functionality to trigger unauthorized transfers. Other forms of drainers may exploit NFT or Token-based triggers to generate fake resources that in turn facilitate the hidden and unauthorized transfer of cryptocurrencies.
Crypto drainers are often provided through a Drainer-as-a-Service model, with DaaS vendors offering software and support to cybercriminals for a percentage of the stolen funds. Services typically offered by a modern DaaS include
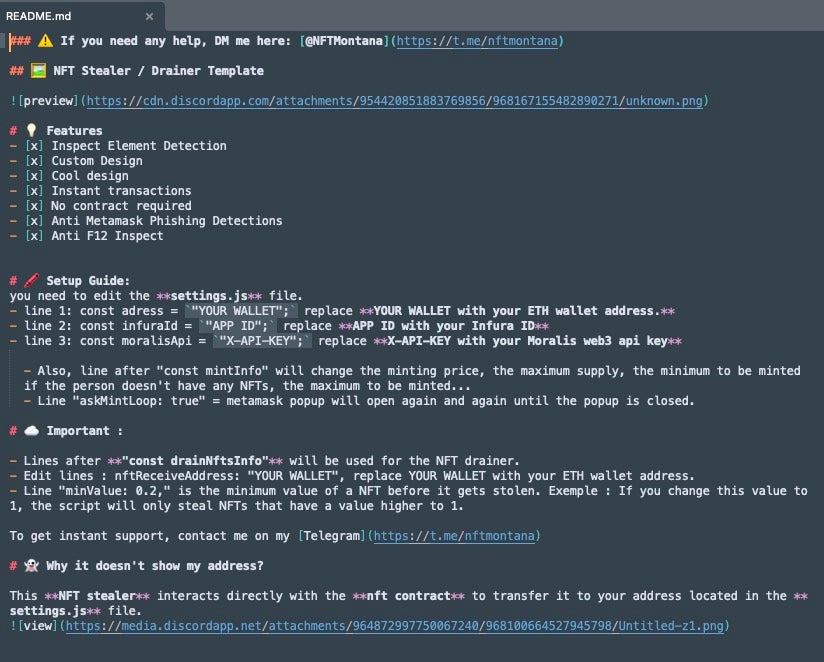
- Turnkey crypto-draining scripts
- Customizable smart contracts
- Phishing kits and social engineering services
- Premium OPSEC or security and anonymity services
- Integration assistance and mixing/obfuscation
- Ongoing updates, maintenance and technical support.
Turnkey or ready-to-use crypto draining scripts, for example, are used to facilitate the automation of draining cryptocurrency from target wallets. They are structured to be simple to understand and deploy, with little to no previous knowledge required.
The stolen cryptocurrency is split between affiliates (users of the DaaS) and the Daas operators. Typically operators take anywhere between 5% and 25% of the cut, depending on the services provided.
The Threat of Account Takeover Attacks
Crypto draining can be hugely profitable for threat actors when they successfully take over high-profile social media accounts and use these to push malicious content to large audiences from what appears to be a trusted source as recently happened to Mandiant and the U.S. Securities and Exchange Commission.

Other high-profile account takeovers include CertiK and Bloomberg Crypto. In late December, it was reported that a crypto drainer stole $59 million from 63,000 individuals using over 10,000 phishing websites.
These attacks typically begin with a brute-force password attack. This involves systematically attempting all possible passwords until the correct one is found. Accounts that lack 2FA or MFA are particularly vulnerable to this kind of attack.
Once an attacker gains access to the account, they are able to distribute phishing links to websites hosting drainers. For example, they may post content from the account offering free NFTs or other rewards to people who visit the site and sign a transaction. Unwitting victims, believing they will receive something of worth, are all too ready to connect their wallets, little knowing that the site contains a drainer script to empty their wallets.
Attackers use platforms like X, Telegram and Discord to spread their phishing links, leveraging the trust and reach of the respected but compromised accounts to target more victims.
Anatomy of an Attack | the CLINKSINK Drainer
In the Mandiant incident, attackers used malware called CLINKSINK, an obfuscated JavaScript drainer lying in wait for victims who fell for phishing links with cryptocurrency-themed lures. These lures often masquerade as legitimate cryptocurrency resources including BONK, DappRadar and Phantom.
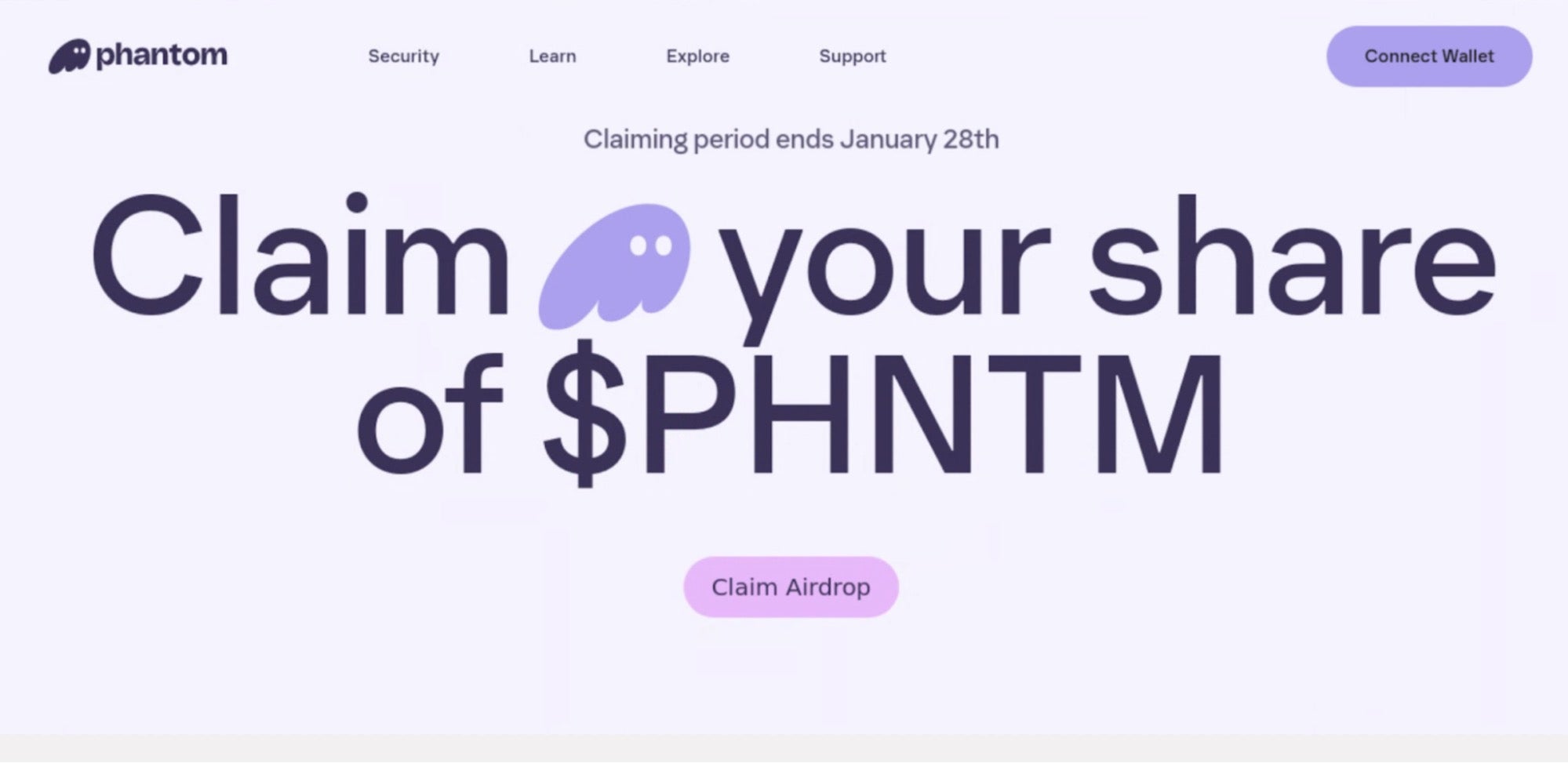
Victims are enticed to connect their wallets in order to claim an ‘airdrop’ – a distribution of tokens or coins to other wallet addresses as a reward or promotion. They are then asked to sign a ‘transaction’ to complete the transfer. This is the crucial step for the crypto thieves as it involves the victim using their private key to authenticate themselves on the blockchain network. If the user completes this step, the crypto draining can then proceed to transfer the contents of the victim’s wallet to their own.
Mandiant says that it identified 42 unique wallet addresses used to receive stolen funds in recent CLINKSINK campaigns like the one associated with its recent Twitter/X account takeover. A number of different DaaS offerings use the CLINKSINK malware, and it is not clear at this time which DaaS may have been involved with the particular incident relating to Mandiant.
Crypto Drainers Are on the Increase
Crypto drainers have become increasingly prominent since 2023 and many are now advertised across underground markets and Telegram channels. Mandiant identified Chick Drainer and Rainbow Drainer as two DaaS offerings using CLINKSINK. However, it is also suspected that the CLINKSINK source code may have leaked and be in use by multiple other threat actors.
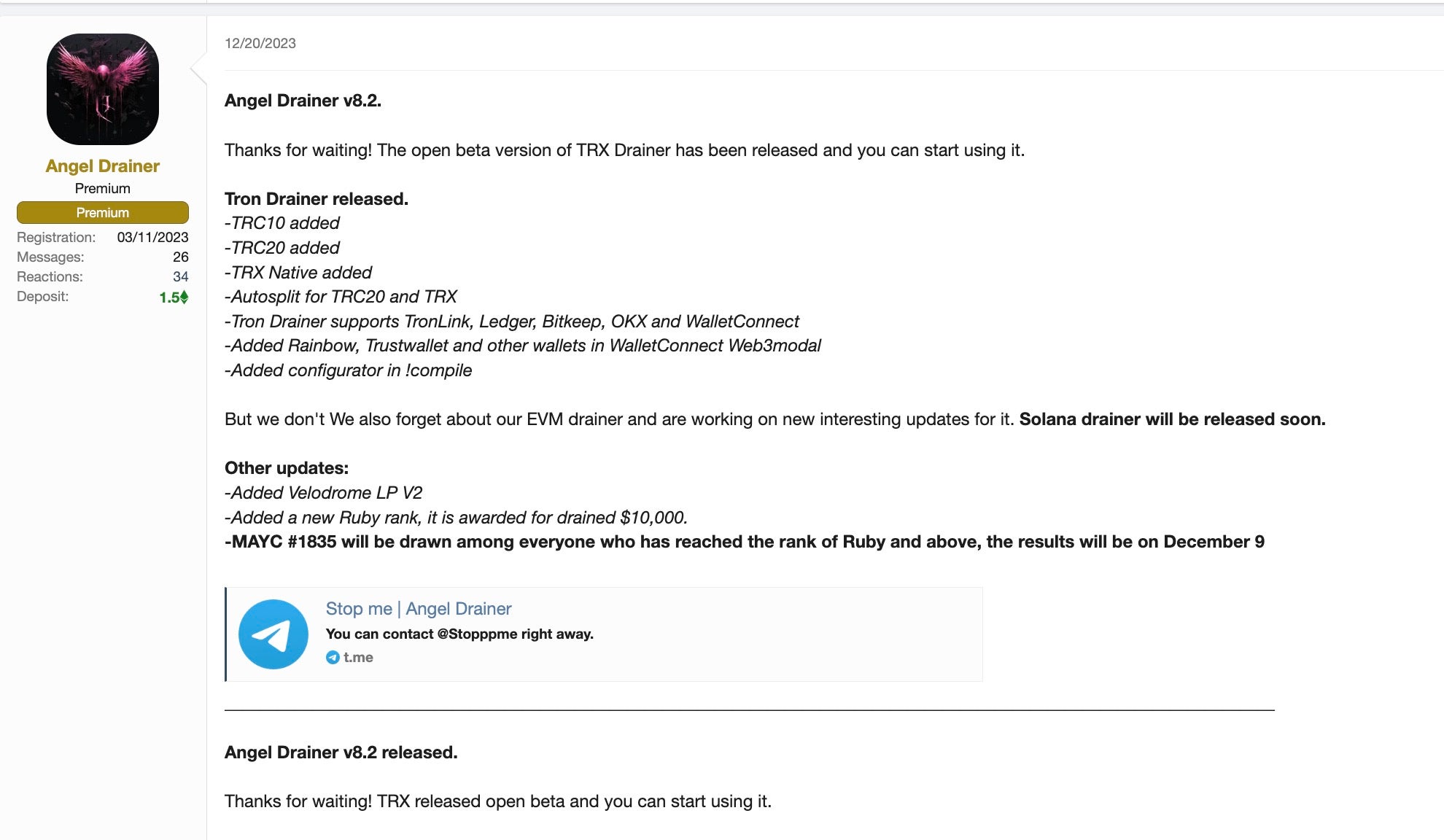
Two other DaaS offerings that are being widely and openly marketed are Angel Drainer and Rugging’s Multi-chain Drainer.
Angel Drainer is a Daas that emerged around August 2023, offering tools and services that were simultaneously advertised across Telegram by known threat actors such as GhostSec. Aside from taking a 20% cut, the operators also require affiliates to make an initial deposit of between $5000 and $10000.
Rugging’s Multi-chain Drainer is another offering that claims to support 20 different crypto platforms. The operators try to entice affiliates by offering low fees, around 5-10% of the affiliates gains.
Preventing Drainer Attacks
Although crypto drainers primarily aim to steal crypto assets from individuals, enterprises and organizations should be alert as their social media accounts can become part of the attack chain. Employees or business units within the organization that deal with cryptocurrency assets could also be at risk.
To combat the threat of attacks from crypto drainers, it is important to ensure that 2FA or MFA is enabled for all social media accounts. Cryptocurrency users are advised to exercise the same kind of caution and be alert for social engineering attempts with NFTs, ‘airdrops’ and other crypto advertisements as they would with emails and other communication channels. Users should also consider adopting hardware-based wallets for added security.
Conclusion
Low skill, low risk, high reward, like Ransomware-as-a-Service (Raas) before it, Drainer-as-a-Service offers those with malicious intent an easy avenue into the crimeware ecosystem. And, as with Raas offerings before, we will not be surprised to see competition among DaaS operators result in a race-to-the-bottom price-wise, tempting even more into malicious activity.
Credentials and access to social media accounts should be treated to the same security considerations as other business services as even temporary access to a businesses’ social media audience can now be used to cause harm much greater than just defacement or denial of service. To learn about how SentinelOne can help protect your organization, contact us or request a free demo.


